New research from Omdia has put hard numbers behind something security teams have been feeling for the past two years: the browser has become the primary attack surface in the enterprise, organizations are investing accordingly, and the results are already measurable.
New research from Omdia has put hard numbers behind something security teams have been feeling for the past two years: the browser has become the primary attack surface in the enterprise, organizations are investing accordingly, and the results are already measurable.
The , based on a survey of 400 IT and security professionals across North America fielded in late 2025, is the most comprehensive industry data to date on how organizations are experiencing, prioritizing, and investing in the secure enterprise browser (SEB) market.
For us at Push, it externally validates what we've known to be true for some time — the browser is where work happens, where attacks land, and where defenders need to be if they want to detect and stop threats before damage is done.
We pulled out seven findings that matter most for security teams evaluating their approach.
1. The attacks driving concern are the ones happening inside the browser session
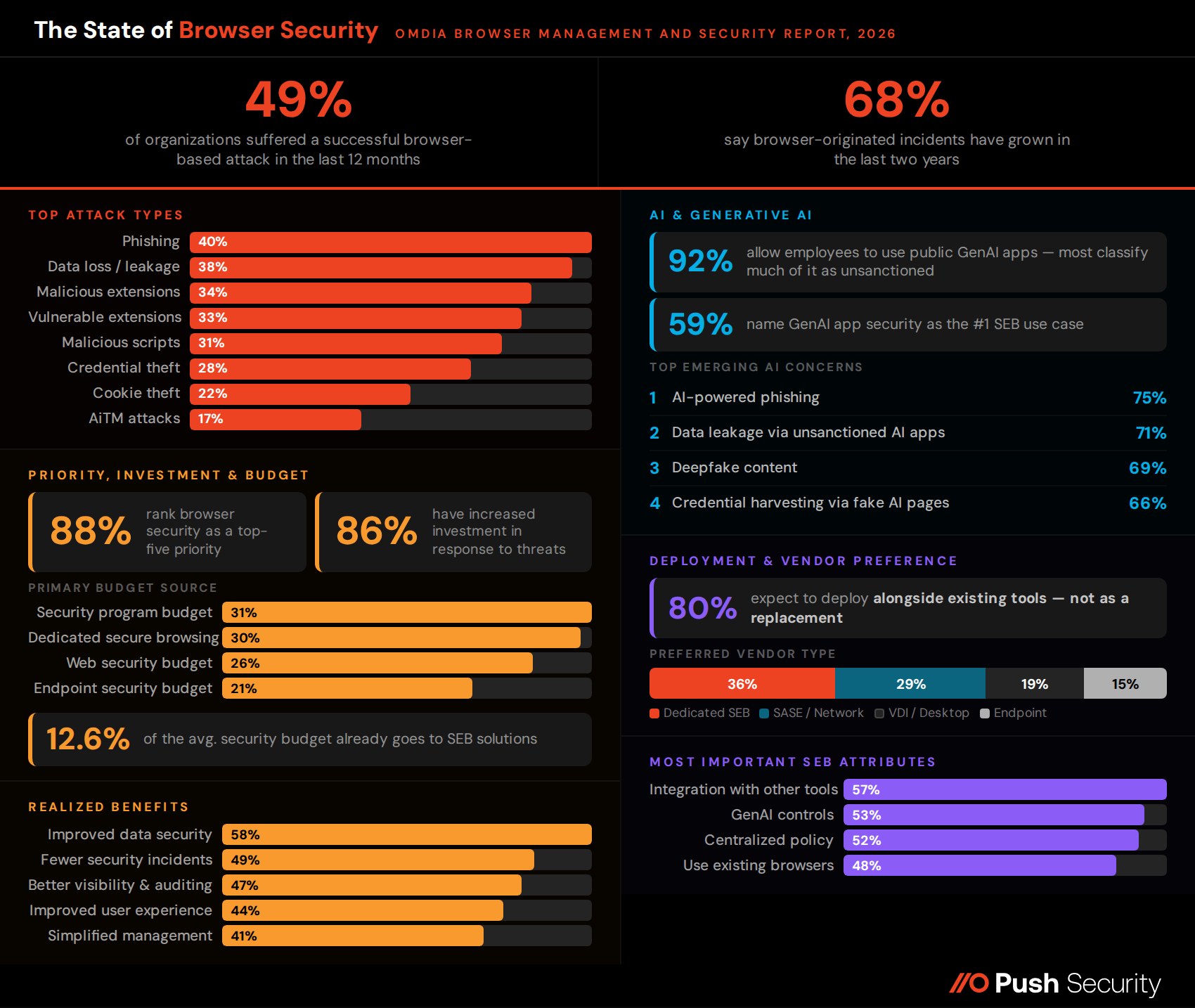
The threat picture is driving everything else in this report, so it's the right place to start. 49% of organizations suffered a successful browser-based attack in the last 12 months. Among those affected, browser-originated incidents account for roughly 37% of all security incidents — and 68% say that share has grown over the past two years.
The browser is not an emerging threat vector. It’s worth noting here that these numbers are also likely lower than the reality, since many are only identified later in the kill chain. Without browser-level telemetry they can be difficult to trace back their source — which in the vast majority of cases, even for malware-driven attacks, is the browser.
The evidence here isn’t just statistics. The real-world breaches attributed to Scattered Lapsus$ Hunters, including the ShinyHunters-branded 2026 hacking spree, clearly underline the real-world threat.
What stands out is that every one of the top attack categories plays out inside the browser session itself — not against the browser as a piece of software, but within the sessions where users interact with applications:
Phishing (40%)
Data loss or leakage (38%)
Malicious browser extensions (34%)
Vulnerable browser extensions (33%)
Malicious scripts (31%)
Credential theft via browser (28%)
Cookie theft (22%)
AiTM attacks (17%)
Phishing, credential theft, cookie theft, and AiTM are attacks that target the user's interaction with a web page — the credential entry, the session creation, the token exchange. Malicious and vulnerable extensions are supply chain risks that operate inside the browser's own execution environment. Data loss happens through the browser when employees upload files, paste data into AI tools, or share information with unsanctioned applications.
None of these are attacks where network-layer traffic inspection, endpoint monitoring, or email scanning provides complete coverage, because the attack surface is the browser session itself.
It's worth noting that AiTM — now the dominant phishing technique in the wild, — shows up at just 17% in Omdia's data. That likely reflects a recognition gap rather than low prevalence: most organizations lack the browser-layer visibility to distinguish an AiTM reverse-proxy attack from a conventional phishing page, which means the real AiTM figure is probably buried inside the 40% who reported phishing generally.
2. Browser security is now a board-level priority
88% of respondents rank browser security as at least a top-five security priority, with more than a quarter (26%) calling it their single top priority. For context, this is a survey that covers the full spectrum of security concerns — cloud, supply chain, AI, insider risk — and browser security has risen above most of them.
This is not aspirational interest. The correlation between priority level and investment is sharp: among those who rank browser security as their top priority, 72% have significantly increased their investment due to emerging threats. Among those who rank it in their top five, that figure is 26%. The organizations that care most are spending the most.
86% of respondents have increased their browser security investment in response to emerging threats, with 36% saying the increase was significant. When you ask what's driving that spend, the answer is the threat landscape: the attacks cataloged in the previous section are the reason budgets are moving.
3. Real budget is being allocated — and it's growing
Secure enterprise browser solutions already take up 12.6% of the average security budget — a substantial allocation for a category that didn't exist as a standalone line item a few years ago. And 85% of respondents expect to increase that spend over the next 12–24 months, with a quarter expecting significant increases.
Where the money comes from tells its own story. The most common funding model is a discrete line item within security program budgets (31%) or a dedicated secure browsing budget (30%). When organizations pull from an existing program budget, web security (26%) and endpoint security (21%) are the most common sources — while SASE/SSE accounts for just 9%, despite SASE vendors being the second most popular vendor category. That disconnect between vendor preference and budget origin suggests the SASE-bundled buying motion may be more aspirational than operational.
IT operations leadership is the top stakeholder in 82% of evaluations, with CISO and security leadership at 64% and CIOs at 42%. Day-to-day management sits primarily with IT Ops (77%) and SecOps (50%). This dual stakeholder picture — IT operations driving evaluation, security leadership providing strategic direction — shapes the competitive landscape in ways we'll come back to.
4. AI is accelerating both the threat and the use case
AI shows up in this report from two directions, mirroring how it is reshaping the security landscape itself.
On the threat side, AI-powered targeted phishing and social engineering is the top emerging concern, cited by 75% of respondents as either very concerning or concerning. Data leakage via unsanctioned AI applications comes second at 71%, followed by deepfake/AI-generated malicious content at 69% and credential harvesting via fake AI or SaaS login pages at 66%. Every one of these threat categories involves the browser — AI-enhanced phishing lands in the browser, AI data leakage happens through browser-based AI tools, and fake AI login pages are browser-based credential harvesting.
[Insight box: This is something we’re seeing extensively in the wild. Just about every phishing kit we encounter today is packed with signs of AI use. You can see our recent analysis of the Doko’s Panel real-time vishing + AitM kit for one example of this. AI development of kits and tools is rapidly driving down the time for attackers to adopt and scale new capabilities — the 37x increase in device code phishing in 2026 being a huge testament to this. ]
On the adoption side, the picture is almost universal — and almost universally under-governed. 92% of organizations now allow employees to use public GenAI applications, and virtually every organization has some kind of policy position: 37% have sanctioned one public app (with everything else unsanctioned), 39% have sanctioned multiple public apps (with others unsanctioned), and 23% restrict employees to a corporate instance while the public versions are unsanctioned.
Even the 8% who don't allow GenAI at all have taken a policy position. Essentially 100% of organizations have a GenAI policy — but for the vast majority, that policy designates a large portion of public AI tool usage as unsanctioned, which raises the immediate question of whether they have the tooling to actually enforce it.
The answer, based on the current tooling landscape, appears to be: not quite. When Omdia asked how organizations currently secure GenAI usage, 58% rely on secure web gateways — tools that see traffic metadata but cannot observe what a user actually does inside a GenAI session — while 57% use secure browsing solutions and 57% use SaaS security solutions.
An SWG can tell you that a user visited ChatGPT, but it cannot tell you whether they pasted your company's source code into the prompt. That distinction — between knowing where data went and knowing what the user actually did — is the fundamental gap that browser-layer visibility exists to close, and it is exactly the gap that makes GenAI policies unenforceable without browser-layer tooling.
The use case data reflects this. When Omdia asked about the most important use cases for a secure browsing solution, generative AI application security came in first at 59%, followed by data loss prevention at 51% and general web security enhancement at 42%. The feature priorities tell a consistent story: AI-powered threat detection and response (52%) and advanced GenAI usage controls and monitoring (41%) were the top two capabilities organizations said would be most important in a purchase decision.
AI is both the top threat concern and the top use case for browser security — and it is a browser problem at both ends, because every LLM interaction, every prompt containing sensitive data, and every AI agent authorization happens inside a browser session.
5. Organizations that have deployed secure enterprise browser solutions are seeing real results
One of the most useful sections in Omdia's report is the benefits data — what organizations that have deployed SEB solutions are actually getting out of them.
The top realized benefit is improved data security, cited by 58% of respondents, followed by fewer security incidents (49%), better visibility and auditing (47%), improved user experience (44%), and simplified configuration and policy management (41%). The picture that emerges is not just a security story but an operational one: organizations are seeing fewer incidents, better visibility, and simpler management alongside the security outcomes.
The 49% who cite fewer security incidents as a realized benefit is the number that matters most here, because it directly connects SEB deployment to measurable risk reduction. Organizations aren't just buying tools and hoping — they're deploying them and seeing fewer successful attacks as a result.
6. The market wants protection in existing browsers, not migration
When Omdia asked what attributes matter most in a secure enterprise browser solution, "ability to use existing browsers" ranked as the fourth most important attribute at 48% — behind only integration with other security tools (57%), controls over generative AI application usage (53%), and centralized policy enforcement (52%).
That 48% figure, combined with 80% of respondents saying they expect to use an SEB solution as an integrated or alongside component rather than a replacement for existing tools, points to a clear market preference: organizations want browser security that works with their existing browser estate, not a migration to a new one.
This is consistent with what we hear from security leaders directly. As Josh Lemos put it: "We looked at the full-stack enterprise browser approach, but converging on a single platform was tough. Push gave me the security instrumentation and context I needed without onerous headwinds." The deployment model matters because it determines adoption velocity — and a tool that requires browser migration introduces friction that delays time to value.
Push was built around this insight from day one. As the secure enterprise browser extension for security teams, Push turns any browser — managed or unmanaged, including agentic browsers — into a telemetry source and control point the moment it's installed. It has been rolled out to 100,000 users in under an hour during normal office hours with zero downtime. That is a deployment model that matches what Omdia's respondents are asking for.
7. Dedicated vendors lead over platform plays
When Omdia asked which category of vendor organizations primarily use or expect to use for secure enterprise browsing, 36% chose a dedicated SEB vendor — the largest single category. SASE/network security vendors came second at 29%, followed by traditional VDI/desktop virtualization vendors at 19% and endpoint platform vendors at 15%.
The dedicated category leads, and the reason isn't just first-mover advantage — it's architectural. The alternative paths each come with structural constraints. SASE and SSE platforms are network-centric: they see traffic metadata and enforce URL categorization, but they can't observe the rendered page inside a browser tab — the DOM structure, the script behavior, the credential entry that distinguishes a legitimate login from an AiTM reverse-proxy kit.
Endpoint platforms that bolt on browser visibility are still anchored to the OS layer, solving for browser exploit prevention rather than in-session behavioral detection of the attacks that actually dominate — phishing, credential theft, session hijacking, extension compromise. And when large platform vendors acquire browser security capabilities, the integration work takes years rather than months, during which detection depth sits in a transitional state.
Dedicated browser-native vendors start from a different premise entirely: the browser isn't a supplementary signal feeding into someone else's SASE pipeline or XDR correlation engine — it is the telemetry source and the control point. The browser is the only place where you get simultaneous visibility into both the attacker's technique and the employee's action within the same session, because the phishing page, the credential submission, the token exchange, and the data exfiltration all happen inside the same tab. No network appliance, endpoint agent, or identity provider log can see all of that, because none of them are present where the interaction occurs.
For security teams evaluating SEB solutions, the architecture matters more than the vendor category label. The capabilities Omdia's respondents ranked highest — integration with existing tools, GenAI controls, centralized policy enforcement, and the ability to use existing browsers — all point toward solutions that deliver detection depth through a lightweight deployment model, without browser migration and without the integration debt of a platform acquisition.
Push Security is the most powerful AI-native security tool in the browser. Think EDR, but for the browser — high-fidelity telemetry and real-time control across every session, on every device, with no browser migration required.
Security teams use Push to detect and stop advanced browser-based attacks like AiTM phishing, ClickFix, and session hijacking; gain visibility and control over AI tool usage across their workforce; harden identities by surfacing credential reuse, SSO gaps, and shadow IT; and support data loss and insider investigations with browser-layer telemetry that other tools can't see.
Book a live demo to learn more.
