ShinyHunters' breach of Instructure is the latest in a sustained series of campaigns leveraging three main browser-based attack vectors. Here's our view of the big picture.
ShinyHunters' breach of Instructure is the latest in a sustained series of campaigns leveraging three main browser-based attack vectors. Here's our view of the big picture.
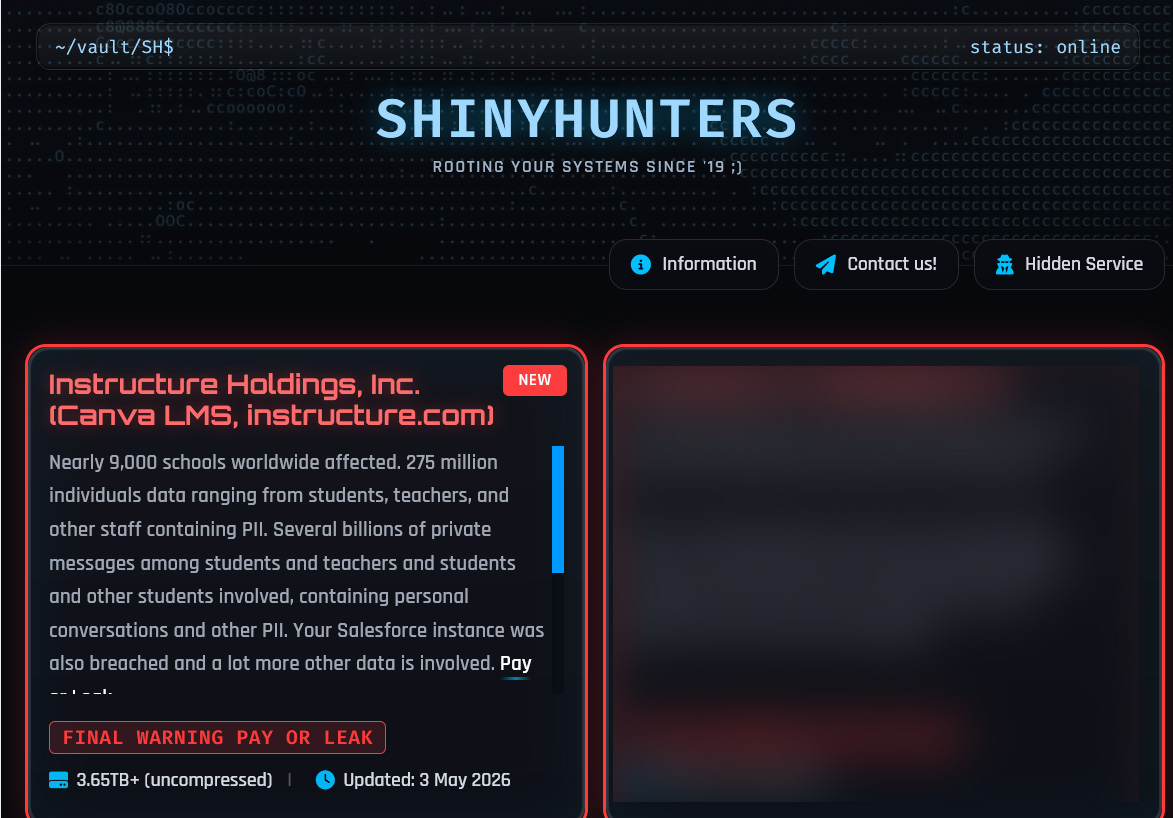
ShinyHunters' breach of Instructure, the company behind Canvas (one of the most widely used learning management systems in education) has escalated rapidly over the past week, with 275 million individuals impacted across 9000 schools worldwide, defaced login portals at roughly 330 schools, and a public ransom deadline.
The human impact is immediate and tangible: students at schools and universities have been unable to access coursework, submit assignments, or sit final exams during one of the busiest testing periods of the academic year, with some institutions sending students home with no clear timeline for when normal operations will resume — the kind of disruption usually associated with ransomware attacks.
This isn’t the first time a cyberattack has caused this kind of disruption to Education — the PowerSchool breach in late 2024 exposed data on 62 million students and 9.5 million teachers across thousands of school districts, demonstrating how deeply the education sector depends on platforms that are now firmly within the crosshairs of organized cybercrime. That was the result of stolen credentials to access PowerSchool’s support portal: another core technique used by ShinyHunters (they demonstrated this at scale in 2024’s Snowflake attacks, using infostealer-harvested credentials to compromise over 165 customer environments).
But the Instructure breach isn't an isolated incident. It’s the latest datapoint in a sustained series of campaigns by ShinyHunters and affiliates of the Com that has, over the past twelve months, compromised thousands of organizations across retail, technology, aviation, financial services, media, gaming, and now education. DataBreaches.net reports that the initial access at Instructure involved social engineering targeting the company's Salesforce instance, which places it squarely within the playbook that Push has been tracking across multiple blog posts since late 2025.
The specific attack vector at Instructure remains unconfirmed, but the documented arsenal of these groups narrows it down to one of three browser-based attacks behind current SLH-related campaigns.
This post examines those three vectors, maps them to the confirmed campaigns and victims that illustrate each one, and explains how browser-layer detection operates at the critical point to detect and intercept these attacks before a breach occurs.
The Com in 2026: a distributed criminal collective
To understand the context behind the Instructure breach, it helps to understand the threat ecosystem behind it. ShinyHunters operates within the SLH (Scattered Lapsus$ Hunters) collective — itself part of the Com, a broader community of English-speaking cybercriminals with international criminal affiliations who collaborate across phishing, initial access, data theft, and extortion operations. The SLH connection traces through a merger of Scattered Spider, Lapsus$, and ShinyHunters, but the Com extends further: groups like Cordial Spider and Snarky Spider, which CrowdStrike characterizes as the new generation of Scattered Spider, are Com members running their own parallel campaigns, even if they are not confirmed as part of the SLH collective itself.
The result is something closer to a distributed collective than a single coordinated group, with several independently operating clusters running parallel campaigns against different target sectors within a compressed timeframe. What connects them isn't infrastructure or coordination, but a shared understanding of where the structural weakness lies in modern business IT, and a common playbook of browser-based attack techniques that exploit it.
Vector 1: Vishing combined with AiTM phishing
The most visible campaign right now pairs targeted voice calls with adversary-in-the-middle phishing pages — an approach that Mandiant, CrowdStrike, and Unit 42 have all documented from the incident response side, and which Push has documented from inside the attacker's own operator panels.
An attacker impersonating IT support calls the target employee, establishes urgency — often citing a "mandatory passkey rollout" or a "security compliance update" — and directs them to a victim-branded AiTM phishing page (typically at a domain like <company>sso.com or <company>internal.com). The attack is processed by a live human in real time, relaying credentials and MFA codes to the legitimate identity provider as they are entered, capturing the resulting session token, and granting the attacker an authenticated session.
One of the reasons that this method is becoming so widespread is the commoditization of effective tools. Push's infiltration of the criminal phishing panels identified over 400 linked domains across four distinct infrastructure clusters. This mirrors the pattern that turned AiTM phishing from a specialist capability into an industrialized market with competing PhaaS platforms, but with the added complication that voice phishing as the delivery vector makes the attack invisible to traditional anti-phishing controls at the email layer.
The speed at which these campaigns execute has compressed dramatically. Unit 42 documented Cordial Spider and Snarky Spider moving from initial compromise to complete data exfiltration in under an hour — fast enough that any detection strategy that relies on human SOC triage will arrive after the data has already left the building.
Vector 2: Vishing combined with device code phishing
The ShinyHunters Salesforce campaign that ran through 2025 and into 2026 used device code phishing as one of its core methods, compromising over 1,000 organizations and claiming 1.5 billion stolen records — including an attempted extortion of Salesforce itself. The attack involved registering an attacker-controlled "DataLoader" application mimicking a legitimate Salesforce tool, configuring it to request broad OAuth scopes including full API access and refresh token generation, and guiding victims through the device authorization flow via vishing calls.
Device code phishing exploits the OAuth 2.0 device authorization grant — a flow designed for devices without browsers, like smart TVs, but used in a wide range of scenarios including CLI logins — by tricking users into entering a code on Microsoft's (or another identity provider's) legitimate verification page. Since the victim is usually signed into the app in their browser, there’s no login at all. They simply navigate to the app’s device code login page and enter an attacker-provided code to grant the attacker an access token.
This is what makes device code phishing structurally different from AiTM: it defeats all MFA (including passkeys) because the attack doesn’t target the login, but the authorization layer instead.
Device code phishing has been rapidly commoditized. What began with Storm-2372's nation-state campaigns in August 2024 has since proliferated through criminal kits like EvilTokens and Venom — which reuses Sneaky2FA's AiTM infrastructure while adding device code phishing options — and more recently through Tycoon2FA, which has adopted device code phishing capabilities alongside its established AiTM functionality. Push now tracks 12+ distinct device code phishing kits in the wild and has measured a 37.5x increase in device code phishing activity since the start of 2026.
Vector 3: OAuth supply chain attacks through compromised integrators
The third vector does not require the attacker to phish the victim organization's employees at all. Instead, it exploits the OAuth trust relationships that organizations create when they connect third-party SaaS vendors into their environments — and the consequence is that every organization that authorized one of these integrations effectively extended its security boundary to include the vendor's own security posture.
The Salesloft/Drift supply chain attack demonstrated this at scale in 2025: in an extension of the previously mentioned device code phishing campaign, the attacker compromised Salesloft's GitHub environment, used TruffleHog to find secrets, stole Drift OAuth tokens, and used them to access downstream Salesforce environments. The same pattern was later repeated at Gainsight.
Along with the previously mentioned device code phishing attacks, more than 1000 organizations were breached. The attackers then harvested AWS keys, Snowflake credentials, and stored passwords from breached Salesforce instances, compounding the access into progressively wider reach.
The same structural pattern has continued into 2026 with the Anodot supply chain compromise, which has produced confirmed breaches at Vimeo (119,000 users), Rockstar Games (78.6 million records), and Zara/Inditex (197,000 people), with further downstream victims likely still emerging. The Vercel breach demonstrates this too, which involved compromised OAuth tokens from Context.ai cascading into Google Workspace, reinforces the same attack pattern (though it was likely not a ShinyHunters operation despite being claimed by someone pretending to be them).
A forgotten SaaS integration can easily become the pivot point for downstream compromise. The moment you authorize a third-party integration, your security boundary extends to include that vendor. If the third-party is compromised, every downstream customer organization with an active integration is exposed.
These attacks all happen in the browser
Every one of these attack chains is a browser-based attack that either occurs in the browser (AiTM phishing, device code phishing) or could have been prevented at the browser layer (OAuth consent governance). The techniques are interchangeable — the same criminal kits now offer AiTM and device code phishing side by side, and the same threat actor (ShinyHunters) has used all three vectors across different campaigns within the same twelve-month period.
How Push can help
Push operates at the exact point in each of these attack chains where automated intervention can still prevent the compromise. For vishing + AiTM attacks, Push's behavioral phishing detection analyzes and blocks the phishing page in real time by detecting it from the user's browser — regardless of the domains used, hosting infrastructure, or where the URL was delivered.
For device code phishing, Push detects the phishing pages associated with device code phishing kits — including generic, technique-class detections that catch new kits without requiring kit-specific signatures. Second, Push provides an additional layer of protection on the legitimate device code authentication pages themselves, preventing users from entering attacker-supplied codes into them. Together, these detections cover both the kit-operated phishing infrastructure and the legitimate auth pages that the attack flow depends on.
For OAuth supply chain attacks, Push's detects and controls OAuth consent flows at the browser layer — capturing which application is requesting access, what scopes it's requesting, and whether the grant should be permitted under organizational policy. Push customers can also block OAuth connection requests as they transit the browser, enabling security teams to stop unwanted integrations being added in the first place.
Closing thoughts
The Instructure breach — and its real-world impact on students, teachers, and families — will produce more details as the investigation progresses, and those details will almost certainly map to one of these three vectors. But the defensive strategy doesn't need to wait for confirmation, because all three converge on the same control point: the browser, where the attack begins or the integration decision is made.
Organizations with browser-layer detection and OAuth controls in place have defense-in-depth against the full range of techniques that modern threat groups like ShinyHunters employ, regardless of the specific vector any given campaign uses.
Push Security is the most powerful AI-native security tool in the browser. Think EDR, but for the browser — high-fidelity telemetry and real-time control across every session, on every device, with no browser migration required. Security teams use Push to detect and stop advanced browser-based attacks like AiTM phishing, ClickFix, and session hijacking; gain visibility and control over AI tool usage across their workforce; harden identities by surfacing credential reuse, SSO gaps, and shadow IT; and support data loss and insider investigations with browser-layer telemetry that other tools can't see. Book a live demo to learn more.
Appendix: named ShinyHunters victims since May 2025
To give an indication of the scale, the following table documents all publicly named victims attributed to ShinyHunters specifically since the Salesforce campaign began in May 2025. It is not exhaustive: ShinyHunters has claimed over 1,000 organizations in aggregate across its Salesforce campaigns alone, and many victims have not been publicly named. This list also doesn’t include the billion-plus records compromised in the 2024 Snowflake breaches. The major ransomware attacks executed against M&S, Co-op, and Jaguar Land Rover claimed by the Scattered Lapsus$ Hunters "brand" also aren't listed below.
Campaign | Began | Named victims | Confirmed impact |
ShinyHunters Salesforce Vishing (vishing + device code phishing → Salesforce connected app authorization) & Salesloft/Drift Supply Chain (stolen OAuth tokens → downstream Salesforce access) | May 2025 | Coca-Cola Europacific Partners, Cisco, Qantas, LVMH, Adidas, Google, Chanel, Pandora, Allianz Life, Air France-KLM, Farmers Insurance, Workday, TransUnion, Stellantis, Kering, Odido, Hallmark, Salesloft (origin), Toast, Avalara, Fastly, Cato Networks, Cloudflare, Palo Alto Networks, Zscaler, Tenable, Elastic, JFrog, CyberArk, Rubrik, BeyondTrust, Proofpoint, Workiva, Mercer Advisors, Beacon Pointe, Ameriprise, Kemper, Udemy, 7-Eleven, Mytheresa, Marcus & Millichap, Carnival, Pitney Bowes, Alert 360, Amtrak, McGraw-Hill, Canada Life | 48 named victims. Confirmed individual impact includes 23M+ records (Coca-Cola), 5.7M records (Qantas), 6.2M customers (Odido), 4.4M consumers (TransUnion), up to 18M records (Stellantis), 13.5M emails (McGraw-Hill), 8.2M emails (Pitney Bowes), 7.5M emails (Carnival). ShinyHunters claims 1.5B+ Salesforce records across 1,000+ organizations total. |
Vishing + AiTM SSO (vishing → AiTM phishing page → SSO session capture → SaaS data exfiltration) | Aug 2025 | SoundCloud, GrubHub, Panera Bread, Match Group, Crunchbase, Betterment, CarMax, Edmunds, CarGurus, Hims & Hers, University of Pennsylvania, Harvard University, Optimizely, TELUS Digital, Crunchyroll, ADT | 16 named victims. Confirmed individual impact includes ~30M records (SoundCloud), ~14M records (Panera), 10M+ records (Match Group), ~20M records (Betterment), 5.5M people (ADT), 1M+ records (UPenn), ~1PB stolen from TELUS Digital ($65M ransom refused). |
Anodot Supply Chain (stolen OAuth tokens → downstream Snowflake/BigQuery access) | Apr 2026 | Anodot/Glassbox (origin), Rockstar Games, Vimeo, Zara/Inditex | 4 named victims (12+ total claimed). 78.6M records (Rockstar Games), 197K individuals (Zara), 119K individuals (Vimeo). |
Other SLH-attributed (misc. vectors including infostealer chains, CI/CD supply chain, SaaS platform compromise) | May 2025 | UK Legal Aid Agency, Mixpanel, Wynn Resorts, Woflow, Vercel, European Commission, Mercor, Medtronic, Instructure | 10 named victims across varied vectors. Notable: Vercel (Lumma Stealer → Context.ai OAuth app → Google Workspace), European Commission (poisoned Trivy GitHub Action → 340GB across 71 EU entities) |
