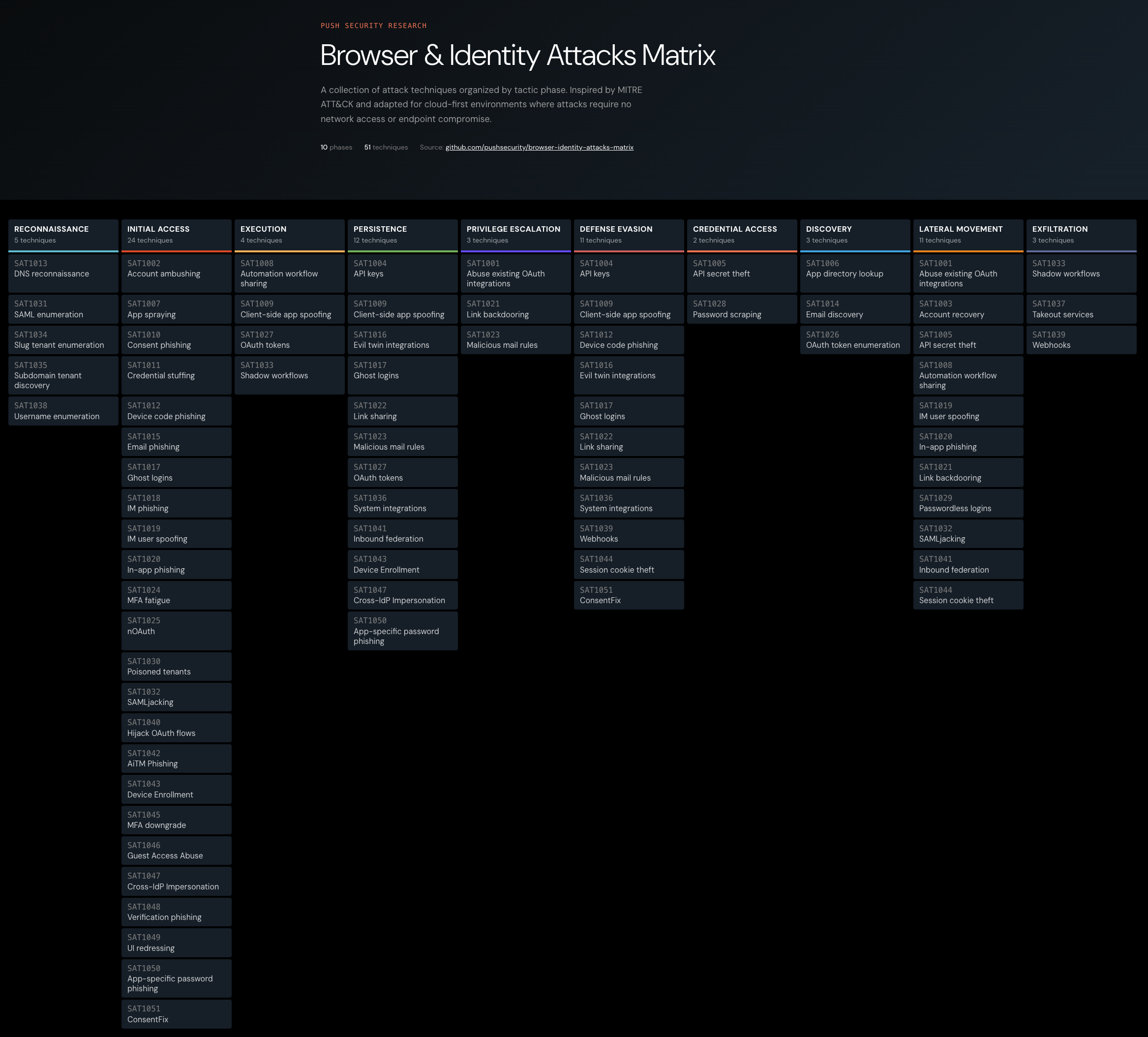
We're re-releasing the SaaS attack matrix as the Browser & Identity Attacks Matrix. Here's why we've decided to make the change and what you can expect to see more of in future.
We're re-releasing the SaaS attack matrix as the Browser & Identity Attacks Matrix. Here's why we've decided to make the change and what you can expect to see more of in future.
When we released the SaaS attack matrix in 2023, we were anticipating a shift that was just beginning to take shape. The techniques that attackers were using to compromise cloud applications and identities weren't well represented in existing frameworks, and many of the ones we documented hadn't yet been widely observed in the wild.
A year later, we reviewed what had changed and found that the initial access phase — the techniques designed to compromise an identity in the first place — was where almost all of the attacker innovation was concentrated. And two years on, that trend has become the story of the modern threat landscape.
Today, we're re-releasing the matrix as the Browser & Identity Attacks Matrix. The name change isn't cosmetic. It reflects that the attacks driving the most consequential breaches are browser-based and identity-first.
Why the scope needed to change
The original SaaS attack matrix was built around a specific insight: that attacks targeting modern business applications played out entirely over the internet, without touching endpoints or internal networks in any way that EDR or network detection tools would recognize.
That framing was useful, and it remains true. But it anchored the matrix to the post-access phase — what attackers do once they're inside a SaaS application — and didn't give enough weight to the initial access techniques that determine whether attackers get there in the first place.
The problem is that initial access is where the overwhelming majority of attacker innovation and investment is concentrated, and the techniques being used to achieve it are best understood as browser and identity attacks rather than SaaS-specific ones. AiTM phishing, ClickFix and its growing family of clipboard-injection variants, device code phishing, OAuth consent abuse, credential stuffing powered by infostealer supply chains, malicious browser extensions all happen in or via the browser.
Another issue is that "SaaS" has arguably ceased to be a meaningful category. When we consider that most organizations run the majority of their business on cloud applications, the difference between what constitutes "SaaS" versus cloud versus just "business IT" is pretty blurry (and feels like an academic rather than practical difference).
So it's less about whether an attack is a "SaaS attack" and more about how these attacks actually play out.
The technique landscape has transformed
The second part to the change is the fact that scale and speed of attacker innovation in the space justifies it.
When we launched the matrix in mid-2023, AiTM phishing was emerging as a serious concern but was far from ubiquitous. ClickFix didn't exist as a named technique. Device code phishing was a curiosity documented by a handful of researchers. ConsentFix was years away from being discovered. Browser extension supply chain attacks were rare enough to be individually notable.
In the two and a half years since, every one of these has become a mainstream, industrialized attack technique — and several have converged in ways that would have been hard to predict.
AiTM phishing has become the default phishing method
AiTM phishing is now the standard, powered by Phishing-as-a-Service kits that operate with the release cycles and customer support of legitimate SaaS products. Tycoon 2FA alone accounted for 62% of phishing detected by Microsoft and over 64,000 confirmed incidents, with Sneaky2FA, FlowerStorm, Evilginx, and a growing roster of competitors filling out the marketplace.
AiTM is constantly evolving, with vendors adding new features, capabilities, detection evasion techniques, and so on. Abuse of legitimate platforms, and increasingly AI-assisted development means that it’s trivial for attackers to spin up and tear down infrastructure, scale their campaigns, target specific organizations with crafted pages and lures, and generally means that attackers can operate highly sophisticated attacks with minimal effort and complexity. This makes AiTM and other PhaaS-powered techniques extremely accessible to all kinds of criminals.
These kits are delivered across several browser-based channels — not just email. Push data consistently shows that roughly 1 in 3 phishing payloads we intercept arrive via social media, search ads, messaging apps, or other non-email vectors.
Vishing has also surged as a delivery channel — CrowdStrike documented a 442% year-over-year increase, and Mandiant found it was the single most common initial vector in cloud compromises at 23%. But the trend that matters isn't voice calls in isolation; it's voice calls combined with browser-based payloads, where a live operator guides the victim into an AiTM page or device code flow that the call alone could not execute.
ClickFix is the top reported initial access vector
ClickFix has gone from nonexistent to one of the most prevalent initial access techniques in under 18 months. Microsoft reported it as the most common initial access vector in 2025, accounting for 47% of observed attacks, while CrowdStrike documented a 563% increase in fake CAPTCHA lures (a top ClickFix style).
ClickFix is admittedly an outlier in a browser attacks matrix — the payload ultimately executes on the endpoint, not in the browser — but the delivery is overwhelmingly browser-based: 4 in 5 ClickFix payloads intercepted by Push arrive via search engines as a result of malvertising or compromised web pages, not email, which means the browser is the only control point that actually sees the attack before the user pastes the malicious command.
ClickFix is now the primary delivery mechanism for infostealer malware, which is in turn the primary source of the stolen credentials and session tokens that power credential stuffing and session hijacking — which means the technique sits at the start of a cycle where one class of browser-delivered attack generates the raw material for the next.
The success of ClickFix has predictably spawned a growing family of derivatives — FileFix, CrashFix, InstallFix — and much of the naming is marketing hype around variations on the same clipboard-injection mechanic. But ConsentFix was a genuinely novel development.
Browser-native ClickFix: ConsentFix
ConsentFix is a fully browser-native attack that merged ClickFix-style social engineering with OAuth consent abuse, compromising accounts through a legitimate Microsoft authorization flow with no endpoint component at all. ConsentFix was traced to APT29 and has since been commercialized on criminal forums, following the same path from state-sponsored technique to commodity criminal tooling that we've seen repeatedly in this space.
ConsentFix demonstrates that the clipboard-injection mechanic can evolve into something that operates entirely within the browser, eliminating the endpoint detection surface that traditional ClickFix still exposed.
Attackers have pivoted to authorization attacks to get around login controls
Authorization attacks like device code phishing have seen a 37.5x increase since the start of 2026, with at least 12 distinct kits now offering the technique. It bypasses standard authentication controls — including passkeys — because the attack occurs through the OAuth device authorization flow rather than the standard login flow.
The technique was first associated with nation-state actors like Storm-2372, but went from espionage-grade to commodity PhaaS tooling in roughly eighteen months, with kits like EvilTokens and Venom now offering turnkey device code phishing as a service.
The device code authorization is effectively performed post-authentication. If you already have an active session in your browser, entering the device code and selecting your account from a drop-down menu is all that's needed. No password or MFA required. You can see an example in the video below.
And the ecosystem is adapting to this opportunity: established AiTM vendors like Tycoon are adding authorization-focused options alongside their existing credential-harvesting capabilities, which points toward multi-technique platforms where operators pick the right tool for whatever defenses the target has in place.
Malicious and hacked browser extensions are one of the fastest growing threats
Malicious browser extensions have matured from an occasional nuisance into a scalable supply chain attack vector. The Cyberhaven compromise in December 2024 — where approximately 35 extensions were weaponized through a single OAuth phishing campaign targeting developers — impacted 2.6 million users and demonstrated that extension supply chain attacks can achieve the kind of reach that used to require a compromised software update server.
Since Cyberhaven, the pace has only accelerated. In 2026 alone, researchers have publicly disclosed at least 250 confirmed malicious browser extensions affecting roughly 1.75 million users, alongside a further 370+ extensions engaged in undisclosed or policy-disclosed data harvesting affecting an additional 44 million users. That doesn't count the extensions from late-2025 campaigns (DarkSpectre, AITOPIA, Trust Wallet) whose impacts carried into 2026.
The attack paths have also expanded. Beyond phishing developers for take over Web Store accounts (the Cyberhaven playbook), attackers are buying existing extensions from developers, waiting for ownership transfers or abandonments to take over, and increasingly vibe-coding their own functional extensions from scratch to build an audience that can later be weaponized. The common thread is that most malicious extensions didn't start out malicious — they started as legitimate tools and were turned into weapons after the fact.
None of this is happening in isolation. The threat landscape has reoriented around browser-based initial access and identity compromise — and the matrix needed to catch up.
The evolution is playing out in public breaches
It’s worth reinforcing that when the SaaS matrix was first released, many of these attacks hadn’t been seen in the wild. The change today is staggering:
When Scattered Lapsus$ Hunters compromised over a thousand organizations' Salesforce tenants through device code phishing, the attack started with a phone call, moved through a browser-based authorization flow for the attacker’s app, and ended with mass data exfiltration via API.
When the same collective launched AiTM phishing campaigns targeting Okta and Entra SSO, the phishing page was operated by a human in real time and delivered over a voice call — not email.
When APT29 deployed ConsentFix across dozens of compromised websites, the entire attack chain was browser-native, abusing a legitimate Microsoft OAuth flow to bypass MFA without proxying a single credential.
The Snowflake breach — arguably the most consequential credential-based campaign of the past several years — saw 165 organizations breached using credentials that had been sitting in infostealer dumps for years, replayed against Snowflake tenants that lacked mandatory MFA. The attack surface wasn't Snowflake's application logic; it was the identity hygiene gap that every organization carries across hundreds of apps.
And that’s just the big picture. Every month we’re tracking new public breaches involving browser and identity TTPs — which again, are just the tip of the iceberg when you consider that many breaches are settled quietly without hitting the headlines.
One of the key drivers here is the shrinking time-to-exploit. CrowdStrike's average e-crime breakout time is down to 29 minutes, with the fastest recorded at 27 seconds. When attackers can move from initial access to data exfiltration within minutes, the window for post-compromise detection collapses to near zero. The best chance of stopping the attack is at the point of initial access before the identity is compromised.
Sidenote: why we're looking at attacks in the browser, not on the browser
Calling this a "browser attacks" matrix needs clarification. We're not talking about browser exploits — RCE vulnerabilities, sandbox escapes, memory corruption bugs. Those attacks target the browser itself, they're extraordinarily expensive to develop, and they're increasingly rare. Browser zero-days hit a historic low of 9% of all zero-days reported to Google, and a Chrome RCE commands a $250,000 bug bounty.
In comparison, a one-year phishing kit rental costs $1,000. A bulk stolen credential list costs $15. An initial-access-broker-provided IdP admin account costs $3,000. When it costs orders of magnitude less to exploit the person using the browser than to exploit the browser itself, attackers will take the cheaper option every time.
It's worth heading off the obvious counterargument: won't AI-assisted vulnerability discovery eventually make browser exploits cheaper? Perhaps — but it will simultaneously make them easier for browser vendors to find and patch, and vendors like Google and Microsoft have the engineering capacity and financial incentive to scale AI-driven remediation far faster than attackers can scale exploit development.
What hasn't changed
The matrix remains open-source, community-maintained, and available on GitHub. The goal is the same as it was in 2023: to give offensive and defensive security teams a shared reference point for the techniques that matter most.
We built it because there was a gap in how the industry talked about these techniques, and that gap still exists — MITRE ATT&CK remains essential for endpoint and network TTPs, but the browser-based, identity-first techniques behind most modern breaches are still underrepresented in traditional frameworks.
We continue to maintain the matrix with input from red teams, detection engineers, and threat researchers across the community. Some of the most valuable additions over the past two years have come from practitioners who encountered a technique on an engagement or in an investigation and contributed it back to the repository.
If you're an offensive security professional using these techniques on engagements, or a defender building detections against them, we want to hear from you. Submit a PR, open a discussion, or flag a technique we've missed on GitHub.
Looking ahead
The pace of attacker innovation in browser-based initial access techniques over the past 18 months has been unlike anything we've tracked before — technique after technique moving from research curiosity to industrialized criminal tooling within months, not years.
AiTM platforms are adding authorization-based attack options alongside their credential-harvesting capabilities.
ClickFix has spawned fully browser-native variants.
AI is lowering the cost of producing convincing social engineering and phishing infrastructure at scale.
We don't see any of this slowing down, and that's exactly why thinking about these attacks as a browser problem instead of siloing them across email, endpoint, network, and cloud categories, each with a partial view of the picture (and still missing the whole when combined).
The Browser & Identity Attacks Matrix is our contribution to keeping that shared understanding current. You can explore the matrix here.
You can also read our recent browser attack techniques report for more information.
Push Security is the most powerful AI-native security tool in the browser. Think EDR, but for the browser — high-fidelity telemetry and real-time control across every session, on every device, with no browser migration required. Security teams use Push to detect and stop advanced browser-based attacks like AiTM phishing, ClickFix, and session hijacking; gain visibility and control over AI tool usage across their workforce; harden identities by surfacing credential reuse, SSO gaps, and shadow IT; and support data loss and insider investigations with browser-layer telemetry that other tools can't see.
Book a live demo to learn more.
