Push Security vs LayerX: Browser security + AI governance in one platform
LayerX covers AI governance and policy enforcement. Push does all of that, and detects the attacks that governance tools were never built to catch.
TL;DR
Push and LayerX are both browser security extensions. The difference is what they're built to do. LayerX is an AI governance and policy enforcement platform. Push is a detection and response platform with the same AI governance capabilities on top. If you need to control how employees use AI tools, both Push and LayerX work. If you also need to detect and respond to browser-based attacks — AiTM phishing, session hijacking, ClickFix, and extension supply chain compromises — Push is the only option built for that.
Side-by-side
Feature comparison
| Feature | Push Security | LayerX |
|---|---|---|
| AI Governance | ||
| Shadow AI discovery | ✓ Yes | ✓ Yes |
| GenAI DLP | ✓ Yes | ✓ Yes |
| AI tool access controls | ✓ Yes | ✓ Yes |
| Agentic browser monitoring | ✓ Yes | ✓ Yes |
| In-session AI visibility | ✓ Yes | ~ Partial |
| OAuth grant monitoring | ✓ Yes | ~ Partial |
| Browser Attack Detection | ||
| AiTM phishing detection | ✓ Yes | ✗ No |
| ClickFix and Fix variant detection | ✓ Yes | ✗ No |
| Session hijacking detection | ✓ Yes | ✗ No |
| AI tools exploited as attack entry point | ✓ Yes | ✗ No |
| Extension supply chain monitoring | ✓ Yes | ✗ No |
| Ghost login detection | ✓ Yes | ✗ No |
| Platform | ||
| In-house threat research team | ✓ Yes | ✗ No |
| Agentic Detection Engine | ✓ Yes | ✗ No |
| Machine-speed detection updates | ✓ Yes | ✗ No |
| Any browser, no migration required | ✓ Yes | ✓ Yes |
| SIEM and IdP integrations | ✓ Yes | ✓ Yes |
Detection vs governance
Governance tells you what's in use. Detection tells you what's under attack.
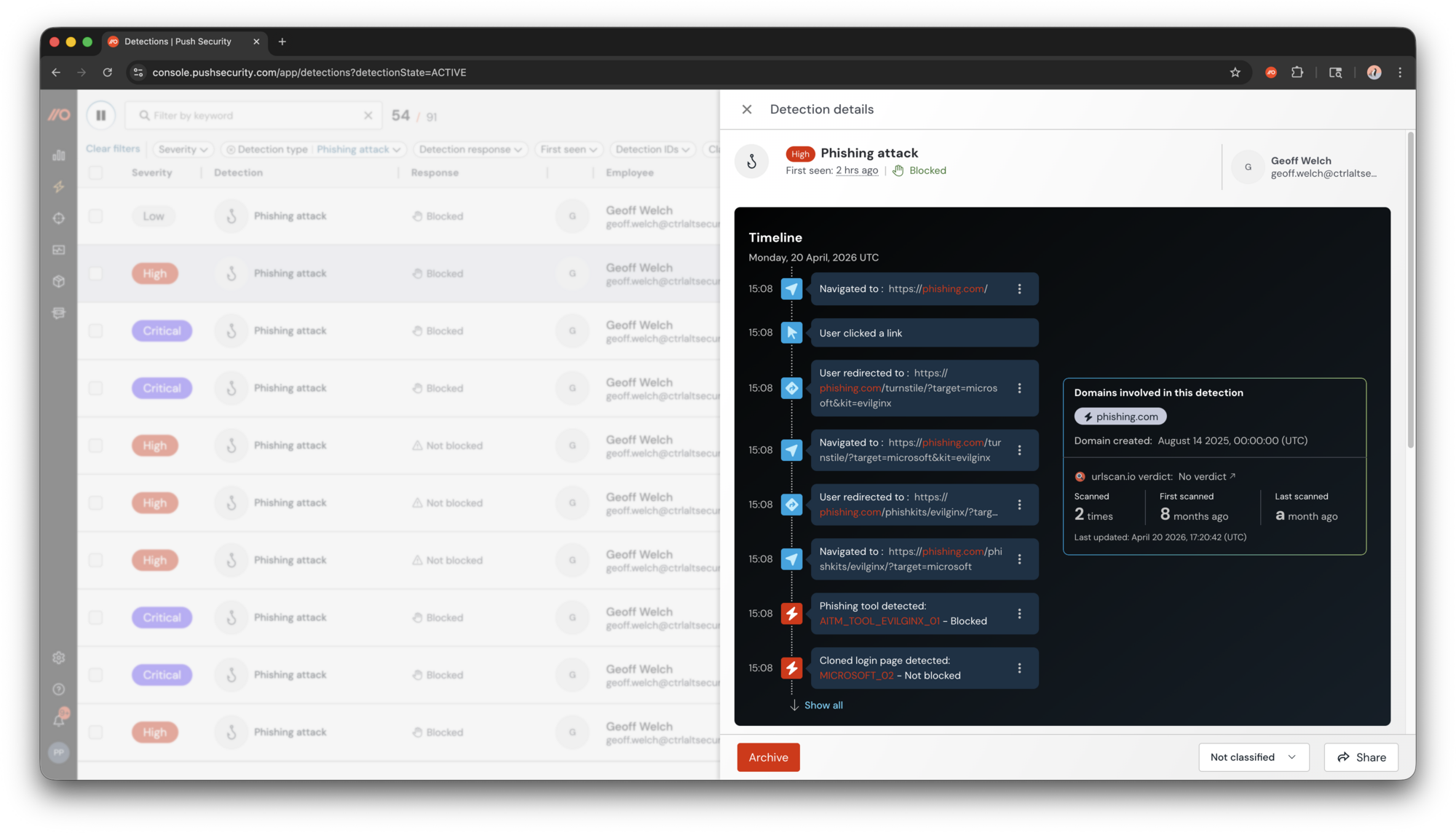
LayerX sees which AI tools are accessed and whether policy is being followed. Push sees that, plus what's happening inside those sessions: prompt content, OAuth grants, data passed to agentic browsers. It also catches the attacker techniques governance tools weren't designed to see: AiTM phishing, ClickFix delivery, and credential theft at a speed and scale that makes policy enforcement the last line of defence, not the first.
Extension security
Risk scoring is not the same as detection.
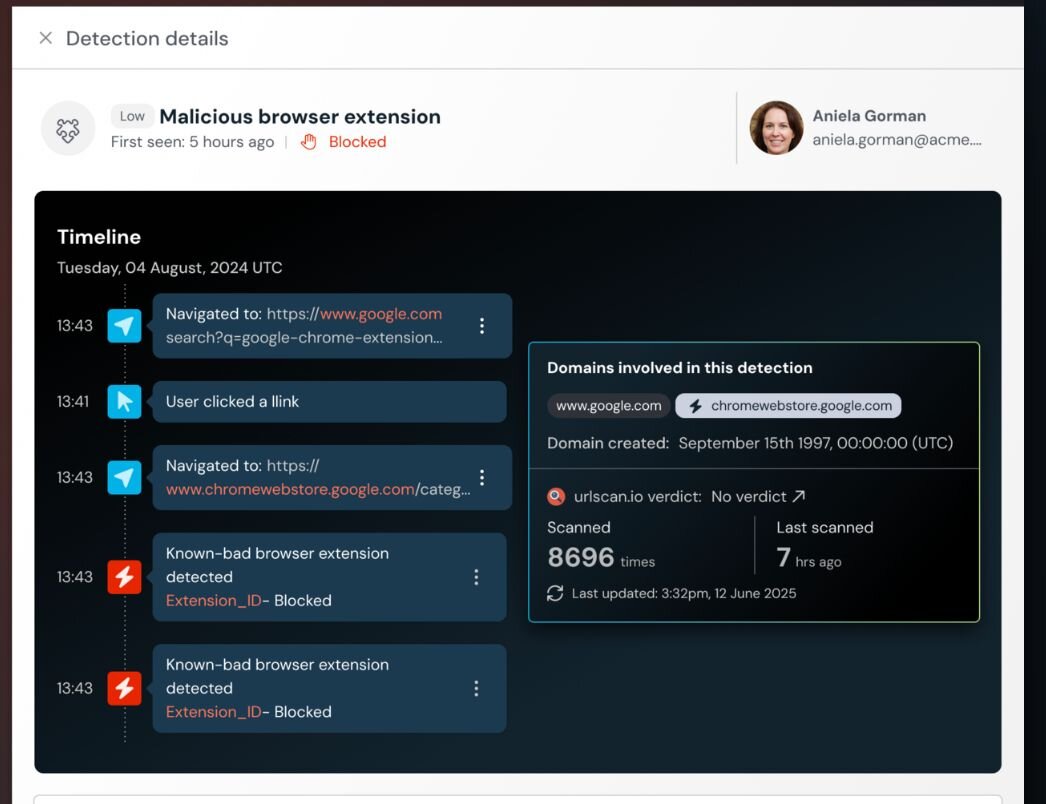
LayerX scores extensions based on permissions and risk profile today. Every major extension supply chain breach of the past 18 months involved extensions that scored as low or normal risk immediately before they were weaponized. Push monitors for the signals that precede compromise: ownership changes, permission escalations, developer account changes. It blocks automatically when a meaningful indicator fires.
Autonomous threat response
The Agentic Detection Engine.
Push's autonomous agents continuously hunt for new attack techniques, write detection rules, and deploy blocking scripts without human intervention. LayerX has no comparable in-house threat research team and no equivalent agent model operating at scale. Detections ship within minutes of a new threat being analyzed, not at the speed of a product release cycle.
See how Push covers AI governance and detects the attacks your current stack can't see.
Buyer scenarios
Which platform fits your use case?
Choose Push Security if…
- Your security team needs to detect and respond to browser-based attacks, not just enforce policy after the fact.
- You're dealing with AiTM phishing, session hijacking, ClickFix, or extension supply chain risk and need behavioral detection, not risk scores.
- You want AI governance and browser attack detection from a single platform, without stitching together two tools.
- You need an autonomous detection layer that keeps pace with attacker techniques without waiting on manual rule updates.
Choose LayerX if…
- Your primary requirement is AI governance and compliance controls, with no immediate need for attack detection.
- You need a policy enforcement layer with audit trail capabilities for regulatory or compliance purposes.
- Minimum deployment size is not a constraint for your evaluation.
Common evaluation questions
Frequently asked questions
How is Push Security different from LayerX?
LayerX is built around policy enforcement: controlling which AI tools employees access, what data moves through them, and whether usage complies with policy. Push does all of that, and adds TTP-based detection and response for browser attacks. The core difference is that LayerX tells you when policy is violated. Push tells you when an attack is in progress.
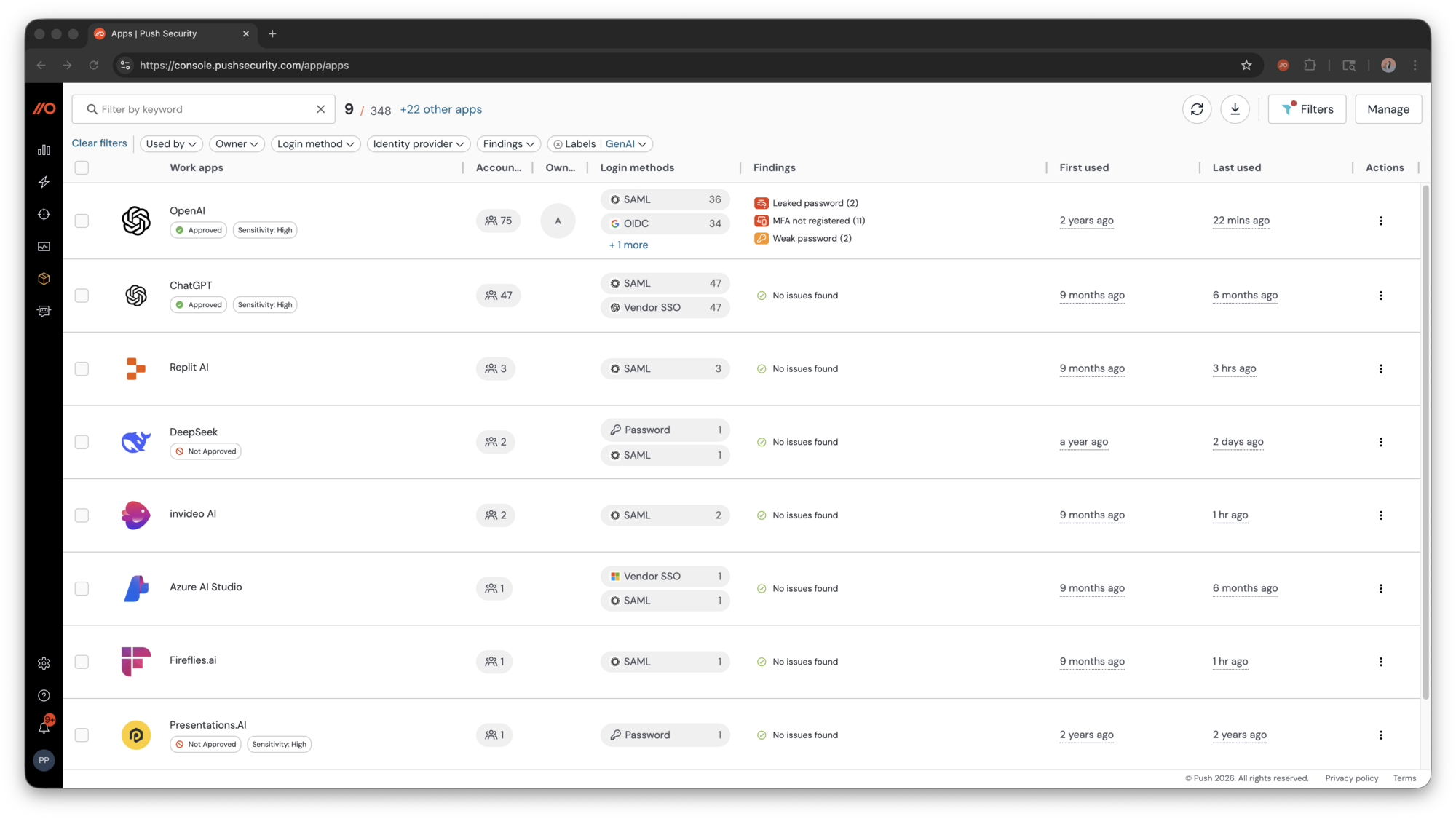
Does Push Security cover AI governance?
Yes. Push covers shadow AI discovery, GenAI DLP, AI tool access controls, agentic browser monitoring, and AI usage audit trails. It also sees what users do inside AI sessions — not just which tools they access — including prompt content and data passed to agentic browsers.
Does LayerX detect AiTM phishing or ClickFix attacks?
No. LayerX uses URL filtering and runtime page scanning to flag known-bad or suspicious content. Push detects attack techniques behaviorally — including AiTM phishing kits, ClickFix lures, and session hijacking — based on how the attack is constructed and executed, not whether the domain or page object is recognized.
How does Push handle browser extension security differently from LayerX?
LayerX scores extensions based on permissions and risk profile. Push monitors for the events that actually precede extension-based breaches: ownership transfers, permission escalations in updates, and developer account changes. The extensions behind Cyberhaven, DarkSpectre, and Trust Wallet all scored as low risk before they were weaponized. Push blocks automatically when a meaningful indicator fires.
Does Push require users to change their browser?
No. Push deploys as a browser extension and works across any Chromium-based browser. No migration, no parallel browser ecosystem, no IT lift required.
What is Push's Agentic Detection Engine?
Autonomous agents that continuously hunt for new attack techniques, write detection rules, and deploy blocking scripts without human intervention. When Push's threat research team identifies a new TTP, detections ship within minutes — not at the speed of a product release cycle. LayerX has no comparable in-house threat research team and no equivalent agent model operating at scale.
How does Push handle agentic browsers like Comet, Atlas, and Dia?
Push monitors agentic browser sessions in real time, flagging anomalous behavior, unauthorized data access, and prompt injection attempts as they occur. It identifies whether an action was initiated by a human or an AI agent — a distinction external tools cannot reliably make.
Is Push Security a CASB or endpoint tool?
Neither. Push is a browser-native security platform, operating inside the browser session itself. It sees what CASBs miss (encrypted in-browser activity) and what endpoint tools miss (attacks that play out entirely in the browser without touching the OS layer).
Ready to see the difference?
See what LayerX can't show you
Push covers AI governance and detects the attacks your current stack can't.