We got an inside look at a phishing panel used in criminal campaigns linked to operators like ShinyHunters and BlackFile. Here’s what we found.
We got an inside look at a phishing panel used in criminal campaigns linked to operators like ShinyHunters and BlackFile. Here’s what we found.
When Push detects and blocks a phishing attack, we take the opportunity to do some additional digging to see what we can find. One recent detection caught our attention due to overlapping indicators linking it to the ShinyHunters campaign combining a real-time operated phishing panel with an AITM payload first reported in January 2026. Recent reporting has also highlighted the BlackFile hacking group using heavily overlapping TTPs that track with our data.
Through a bit of digging, we’ve directly accessed active deployments of the operator panels driving these campaigns, observed what happens in real-time when a victim is targeted, and analyzed multiple variants and forks of the tooling.
We’re highlighting four distinct infrastructure clusters associated with this tooling, with each deployment having its own panel implementation. While the panels share common heritage, the operators deploying them appear to be separate groups with different infrastructure preferences and operational patterns.
The existence of these independently branded forks indicates that the tooling has entered a phase of wider distribution — operators who obtained the original panel source are now customizing and reshipping it for their own purposes. As a result, the tooling is now most likely accessible to a broad population of financially motivated threat actors. In total, we’ve identified over 400 domains linked to the attacks.
It’s easier than ever for attackers to spin up and tear down their phishing infrastructure by abusing a range of legitimate services. This is why we’re focused on detecting the actual malicious page at the end of the chain, regardless of the hosting, infrastructure, or delivery vector.
This is extra useful in this case when we consider that a phone call is the delivery vector — not something that typically email-based phishing controls would be able to intercept.
Background
Since at least August 2025, attackers have been running hybrid social engineering campaigns targeting hundreds of organizations across financial services, technology, cryptocurrency, healthcare, hospitality, and private aviation.
August 2025: Tooling made available, used in crypto-focused attacks
November 2025: Major attacks on enterprise identity platforms begin
January 2026: Public breaches reported
March 2026: Activity spikes again
The attacks combine voice phishing with MFA-bypassing adversary-in-the-middle (AiTM) phishing mechanisms that allow the attacker to steal authenticated sessions for target applications — typically enterprise identity providers and cryptocurrency exchanges. Once an identity provider account is compromised, the attackers pivot across connected SaaS platforms — SharePoint, Salesforce, DocuSign, Slack — exfiltrates data, and attempts to extort the victim organization.
Resulting breaches have already been publicly confirmed at SoundCloud (30 million records), Match Group (Hinge, OkCupid, and Match.com — over 10 million records), Betterment (20 million records), and Crunchbase, among others — all linked to ShinyHunters-branded extortion demands. The group also claimed breaches at Bumble, CarMax, Panera Bread, Harvard, the University of Pennsylvania and others in the same period, using data stolen in the Salesforce breaches in 2025 to identify victims and make the social engineering more convincing.
Inside the panels: what Push found
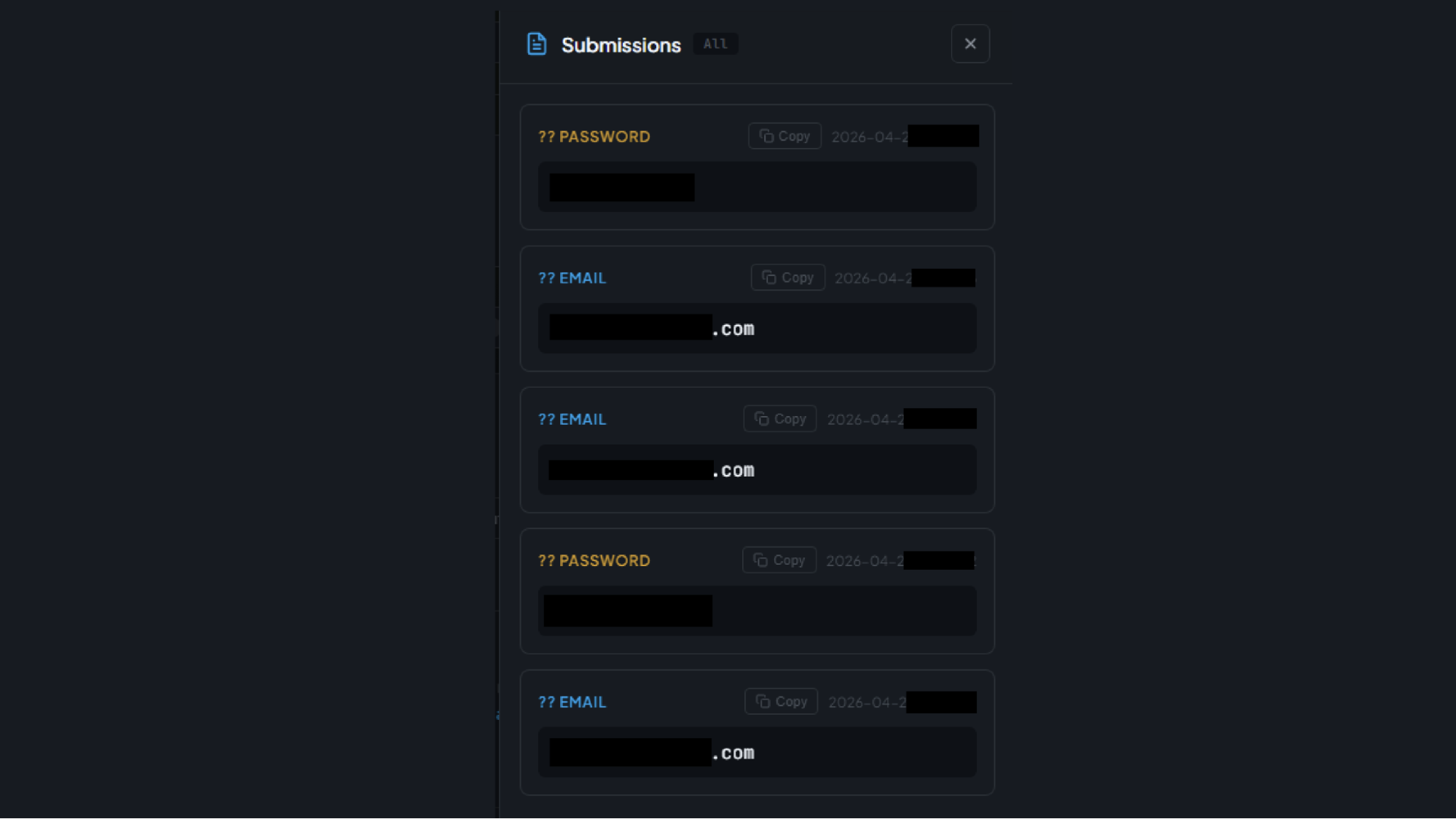
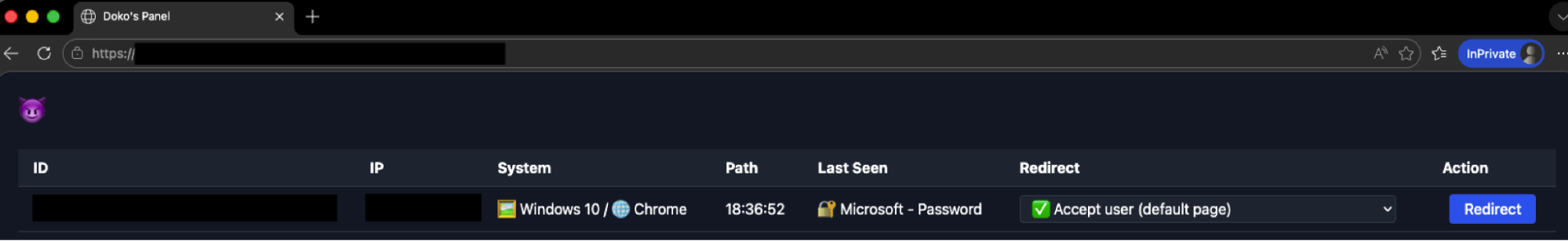
Push detected an active Okta phishing site with TTPs aligned to the tooling used by SLH and affiliated groups. Through analysis of the phishing infrastructure, we gained direct access to Doko’s Panel and variants, and were able to observe how these attacks unfold from the operator's perspective — including real victim submission logs from the current week confirming ongoing active operations.
Doko’s Panel, which takes its name from the Telegram alias of its developer, was linked to ShinyHunters attacks earlier this year. The same persona behind Doko's Panel has been observed actively recruiting "experienced callers" via Telegram, specifying requirements including fluent English with no accent, and advertising six-to-seven-figure weekly returns — evidence of the professionalized vishing-as-a-service model that complements the phishing kit ecosystem.
How the attack works
The general sequence of steps is the same across the panels:
The operator calls the target spoofing the organization's IT helpdesk number, often referencing real employee names or internal ticket numbers to establish trust. The target is directed to a phishing domain — usually following a combosquatting pattern like my<target>internal[.]com or <target>sso[.]com — under the pretext of a mandatory security update, passkey enrollment, or support ticket resolution.
The victim lands on the phishing domain and is presented with a loading spinner — the anti-bot gate that prevents unauthorized access to the phishing pages.
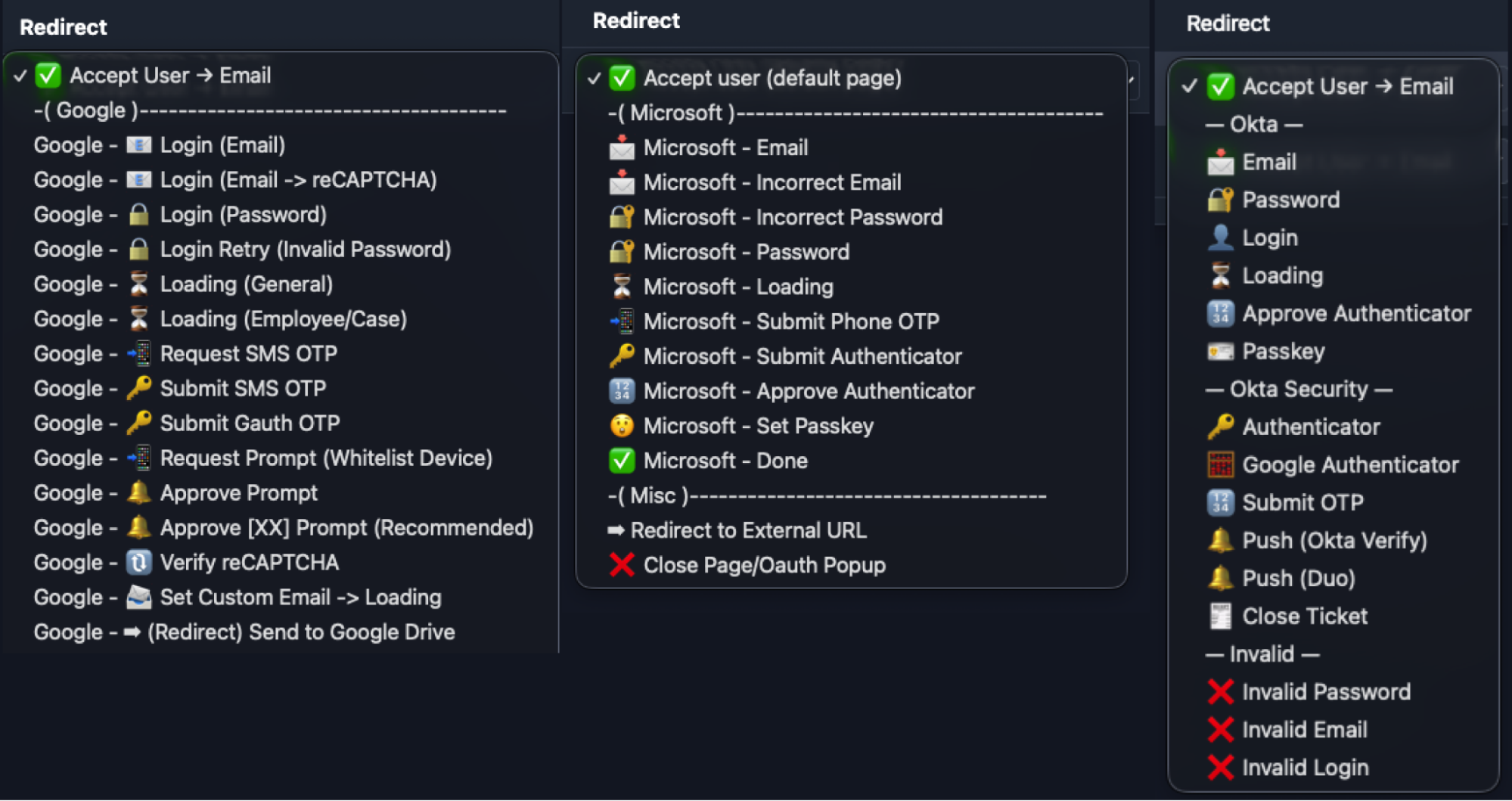
The operator accepts the visitor from the admin panel and the victim is redirected to the cloned login page (e.g. Google, Microsoft, Okta).
The victim enters their email address and password, which is forwarded to the operator's Telegram channel. The victim sees a processing spinner on the branded login form.
The operator relays the credentials to the real identity provider. If they're valid, the attack proceeds. If they're invalid, the operator can redirect the victim back to the credential entry pages. Assuming MFA is required, the operator issues a redirect to an appropriate MFA capture page — "Submit SMS OTP," "Submit Gauth OTP," or "Approve [XX] Prompt," depending on what the legitimate IdP is presenting.
The victim submits their OTP or approves the push notification and the operator relays the OTP in their own login session, completes authentication, and captures the session.
The victim is redirected to a benign page (e.g., Google Drive) or to a support ticket closure screen displaying a fabricated ticket number.
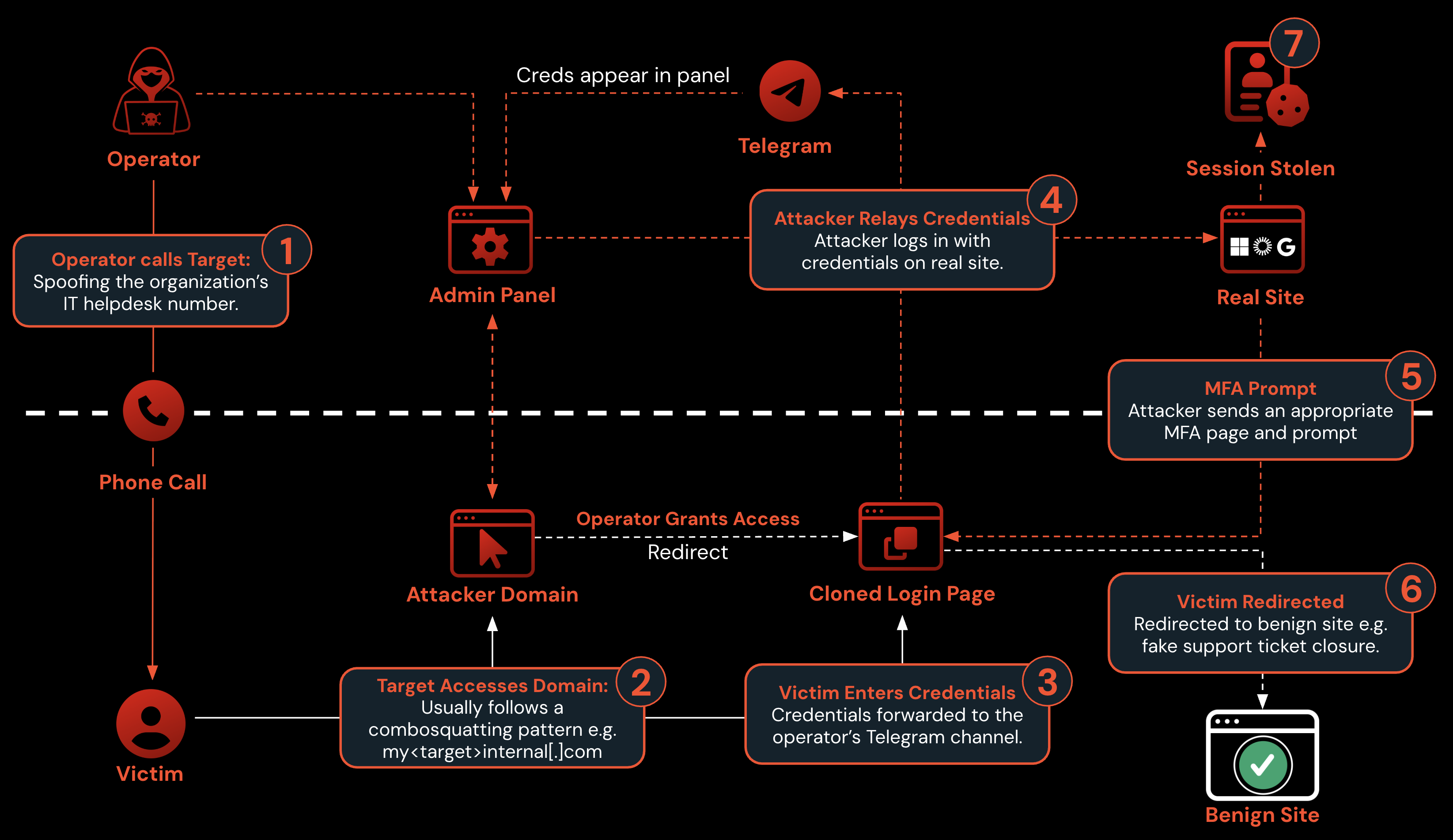
Functionally, this is the same as a typical AITM attack — except that the stages are performed manually by the attacker instead of automatically proxying the victim’s inputs to the real site.
This seems like an odd choice. On one hand, this is a very sophisticated version of a voice phishing attack. But on the other, it’s not taking advantage of some of the standard capabilities that common AITM kits have. This more manual approach is something that Scattered Spider were known for during the 0ktapus days. But it doesn’t make much difference to the outcome, or what we can observe to detect the attack in the browser.
Doko’s Panel
Let’s take a closer look at the panels themselves. We'll start with the default version of Doko's Panel since it’s the most established. It provides a multi-functional framework targeting users of Google, Microsoft Entra, Okta, and popular cryptocurrency exchanges including Abra, Coinbase, Gemini, and Kraken. Its core functionality resides in a client-side JavaScript file (client.js) that establishes the real-time feedback loop between the victim's browser and the operator's C2.
The technical indicators that characterize Doko's Panel in its standard form include:
client.js containing a pingServer() function that sends a JSON POST request to /backend.php every second with the structure { action: 'ping', token, window_id, page, os, browser }. If the response contains a redirect key, the victim's browser navigates to that path.
sendTelegramMessage() (aliased to sendtg()), a function for relaying real-time credential submissions and session updates to the operator's Telegram channel.
backend.php as the primary server-side handler for both victim ping actions and admin panel operations (retrieving connected victim information, sending redirect instructions).
j.php as the endpoint for sending Telegram messages, relaying captured credentials and session logs.
Push found that deployments of Doko's Panel had minimal security by default — anyone was able to view the admin panel and manage visitors' connections without authentication.
Panel proliferation and remixes
Access to Doko's Panel has clearly proliferated beyond its original developers, resulting in remixes and variants being distributed across the ecosystem. Push identified a variant titled "Lord Mensius's Panel" targeting Koinly (a cryptocurrency tax platform), and another titled "$$$" using a template impersonating the Australian Tax Office, also targeting cryptocurrency tax filing.
The existence of these independently branded forks indicates that the tooling has entered a phase of wider distribution — operators who obtained the original panel source are now customizing and reshipping it for their own purposes. As a result, the tooling is now accessible to a broad population of financially motivated threat actors.
heartbeat/check_redirect variant
In addition to Doko’s Panel and its forks, the site initially detected by Push used a modified variant of Doko's Panel with a different C2 protocol. Rather than the standard ping action, this variant sent two types of regular requests from client.js to the backend:
Heartbeat — POST to backend.php with action=heartbeat along with page, token, and window_id.
Check Redirect — GET to backend.php with parameters action=check_redirect along with token and window_id.
A redirect instruction in response to either request causes the victim's browser to navigate to the specified page. The variant compounds this with a separate inline script embedded in the landing gate HTML — in addition to client.js — that schedules its own sendHeartbeat() and checkRedirect() functions on regular intervals.
The result is that the victim's browser sends two pairs of duplicate requests every few seconds (with the inline script transmitting heartbeats in JSON format rather than HTML form-encoded data). This level of broken duplication indicates an inexperienced developer making modifications to unfamiliar code — a pattern reinforced by the LLM-generated artifacts discussed later.
Additional technical differentiators for this variant include:
UUID generation using Math.random() to replace x in the template xxxxxxxx-xxxx-4xxx-yxxx-xxxxxxxxxxxx, rather than the original Doko's Panel method of constructing a template from [1e7]+-1e3+-4e3+-8e3+-1e11 and replacing [018].
No central Telegram sending function, though j.php still exists and is called from inline scripts on individual phishing pages.
No use of FNV-1a to hash-generate the window ID.
Push also found sub-variants hosting Okta phishing pages with additional modifications: a minified client.js script, and a renamed backend endpoint (api_FyekIDWY.php replacing backend.php).
Revamped admin panel
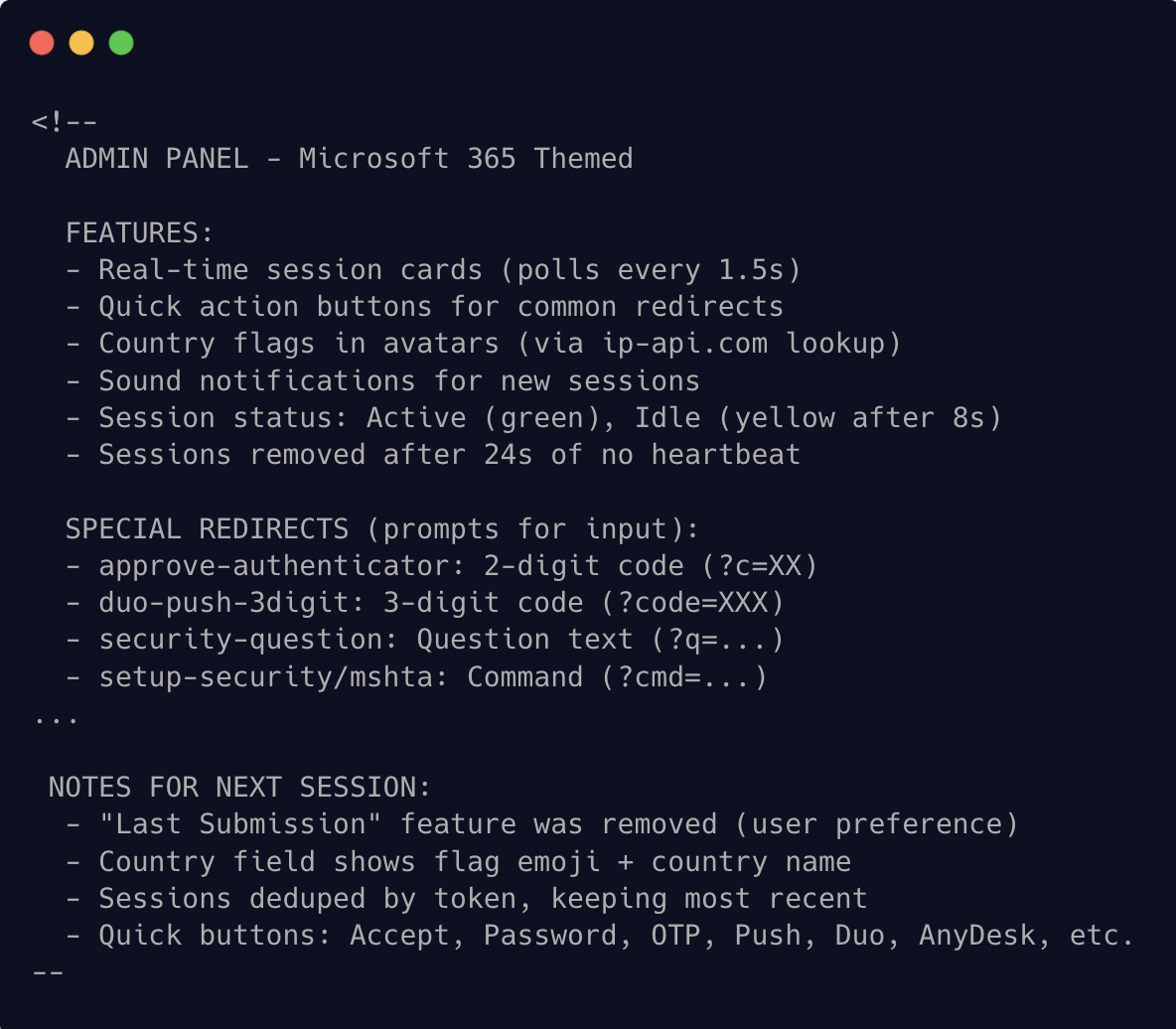
Push also found examples of a significantly revamped admin panel, including a version from April 2026 specifically targeting Microsoft as an enterprise identity provider.
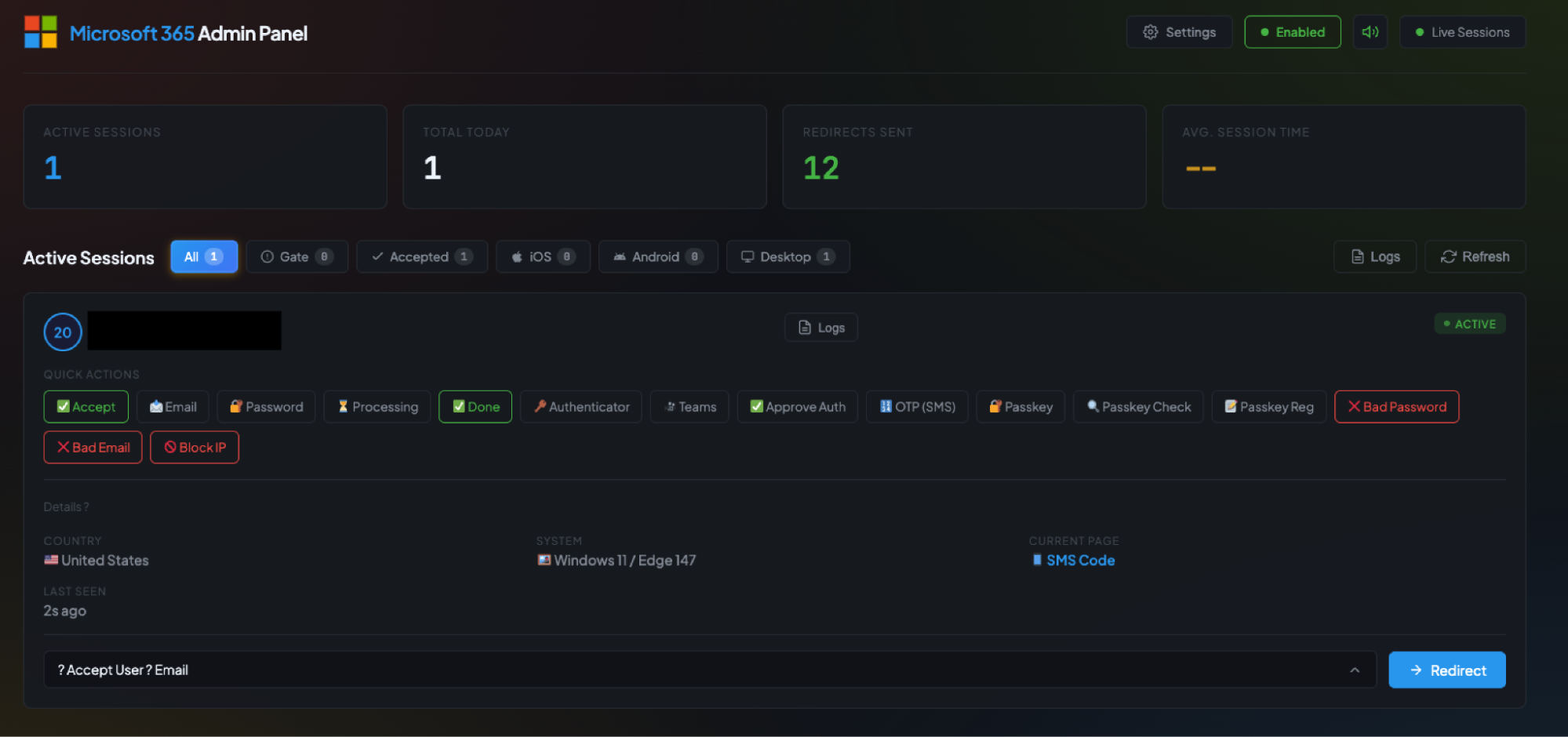
This panel featured a more sophisticated operator interface with an updated look, quick action buttons, and sound notifications.
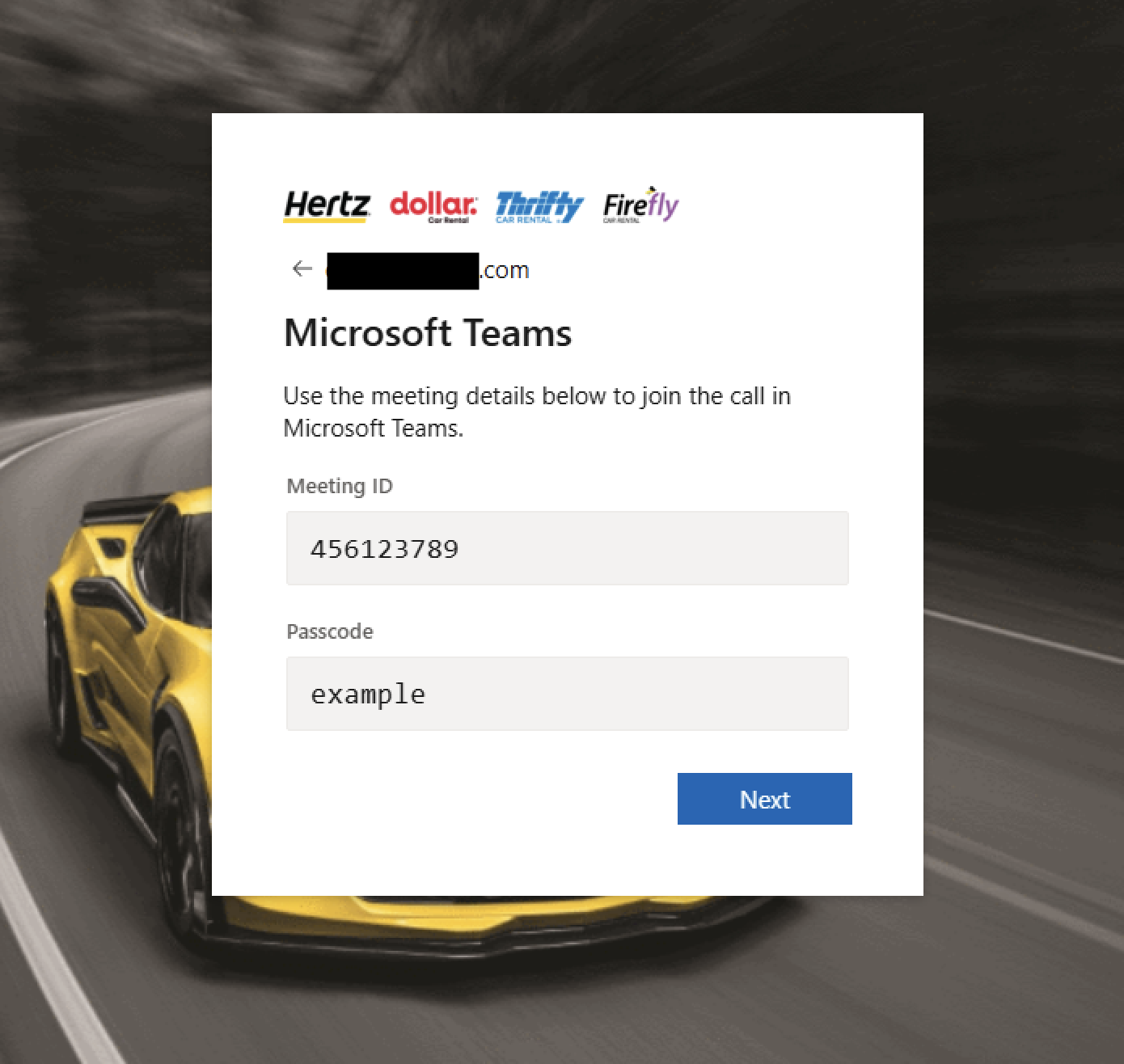
In addition to the standard compromise flow for acquiring email, password, and OTP, this panel provided operator actions for sending Microsoft Teams call instructions to the victim — a Meeting ID and Passcode rendered on a branded page. This capability likely enables further interaction through a channel that supports screensharing, extending the attacker's reach beyond credential theft into live session manipulation. It also has the potential to make the scenario more believable for the victim.
Other capabilities were referenced in the panel's source code but did not appear active in the observed deployment:
Additional MFA approval pages for Duo and Okta, with the operator providing a code to display to the victim.
A code execution prompt to instruct the victim to run a command — the placeholder example being mshta to execute a remote HTA file, suggesting a potential bridge from identity compromise into malware delivery.
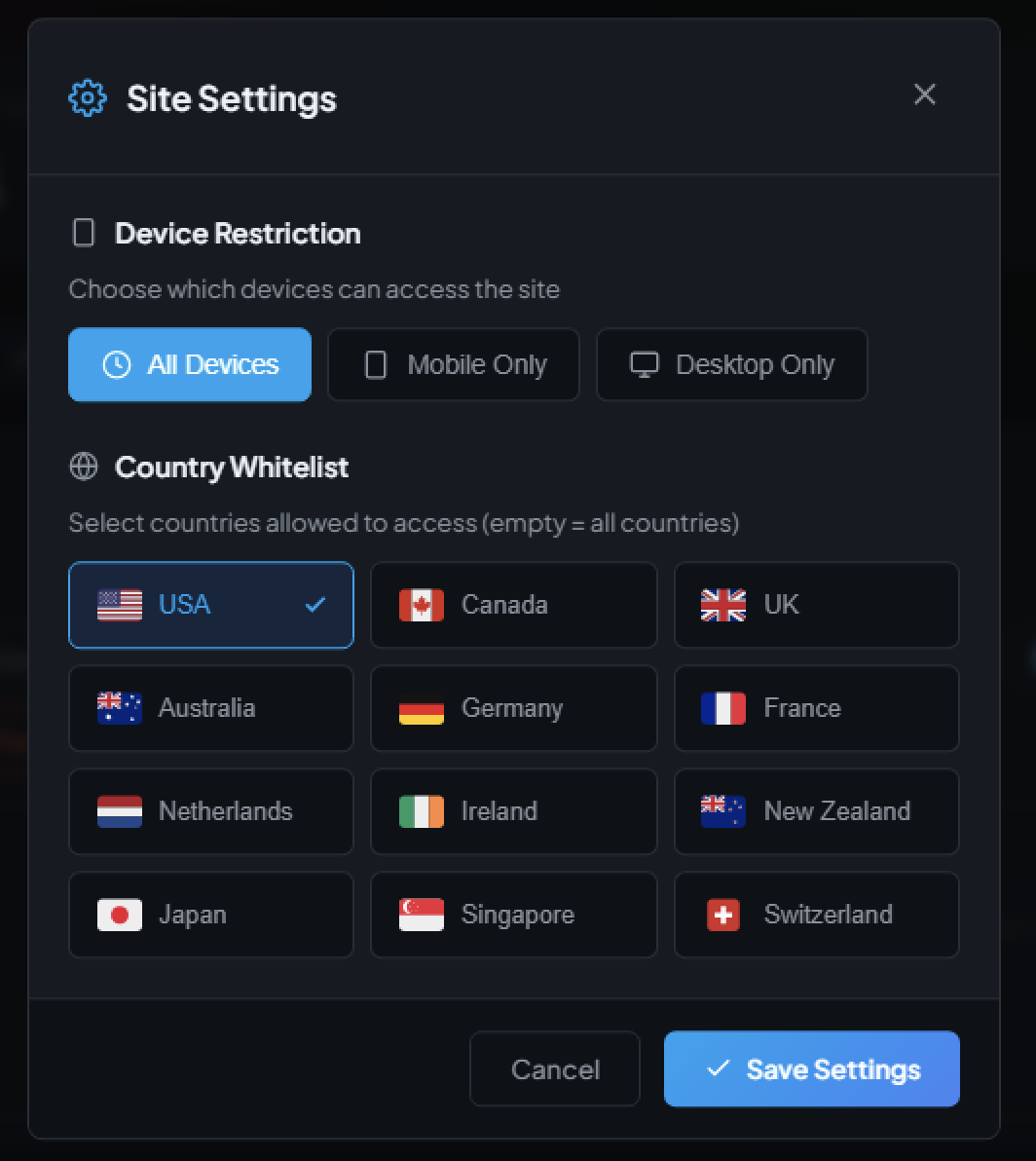
The admin panel also included settings for restricting access to specific geographic locations and device types, allowing operators to refine their campaign targeting and also avoid detection from unusual devices (often an indicator that the visitor is not a real human and is actually a security tool or bot).
LLM-generated tells: vibe-coded phishing infrastructure
Evidence of extensive LLM use is extremely prevalent in attacks detected by Push, from LLM-generated phishing kits and tools to vibe-coded cloned pages. Attackers have also been observed leveraging AI–assisted capabilities in SaaS platforms to automate and scale-up their campaigns from an infrastructure and operations perspective.
The ‘heartbeat’ variant in particular has significant tells of heavy use of LLMs to modify the phishing panel for the operator’s needs. The fact that these are so blatant increases the belief that these tools are being vibe-coded by relatively inexperienced developers with limited regard for operational security.
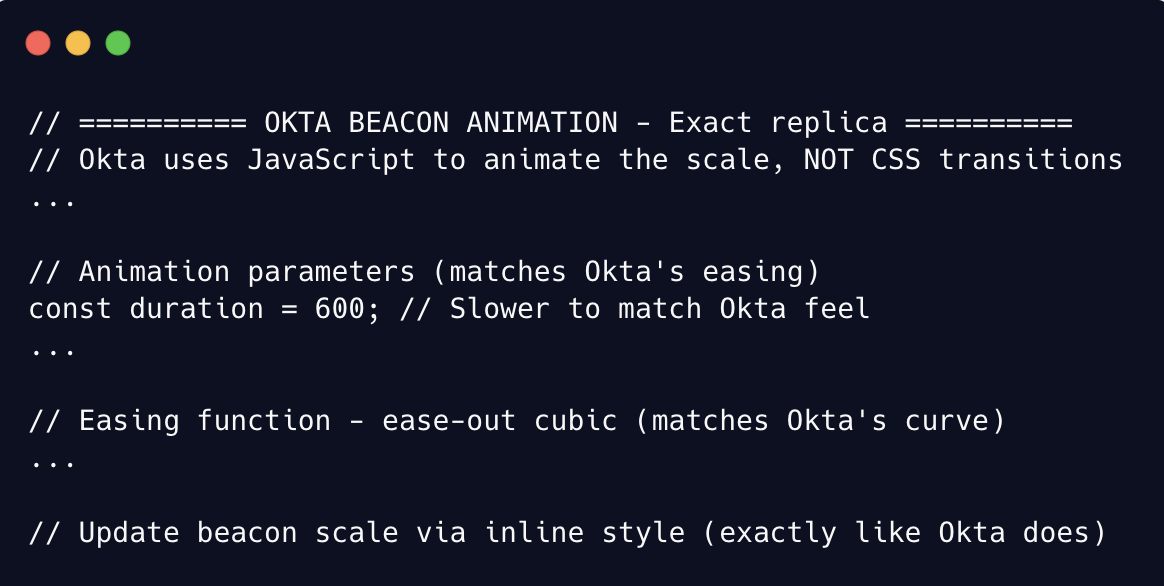
Some versions of client.js begin with verbose header comments that no human developer would write:
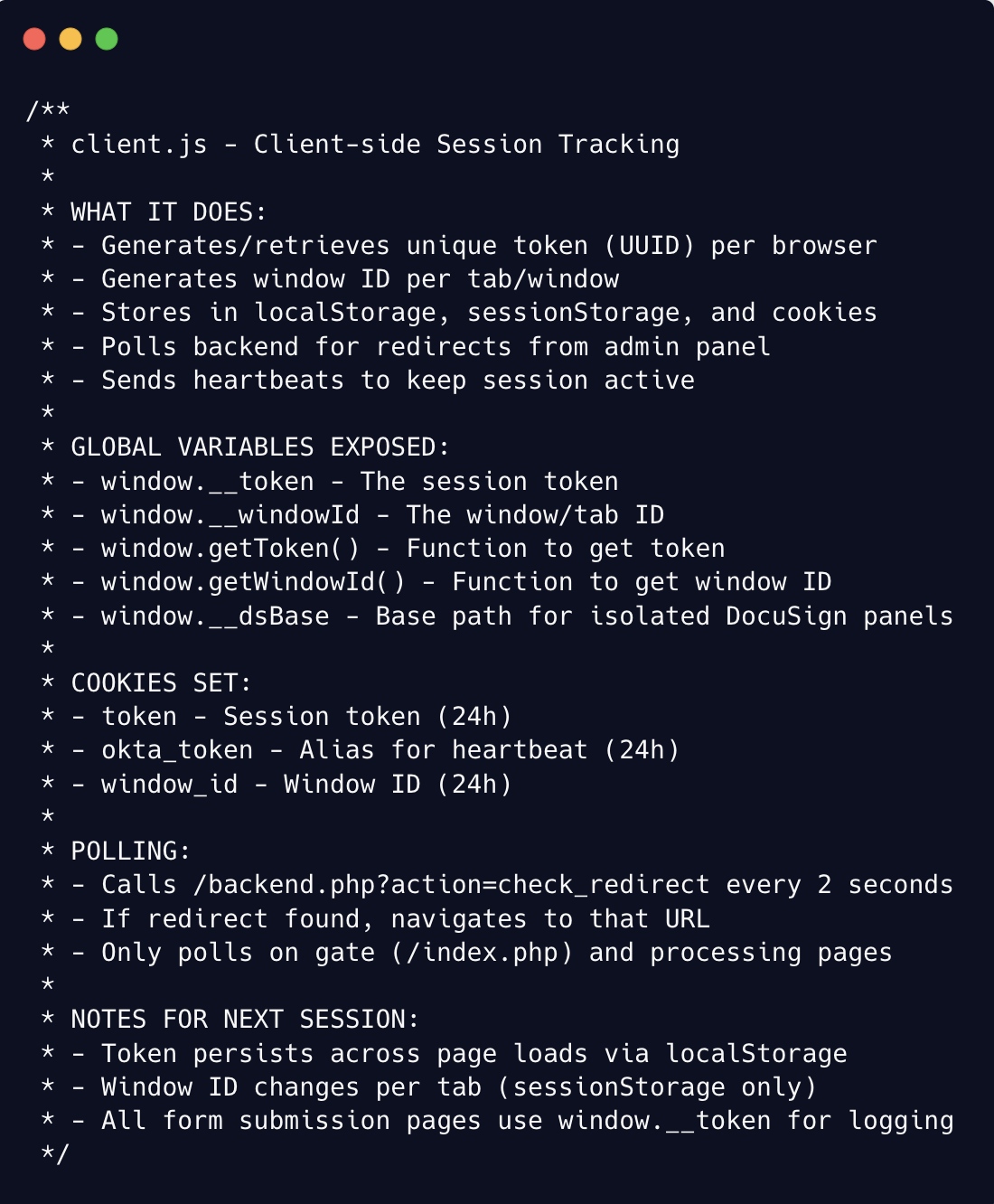
The "NOTES FOR NEXT SESSION" header is particularly telling — it's a pattern generated by LLMs that maintain context between chat sessions, not a convention any human developer would adopt in production code, let alone in a phishing kit where operational security should discourage self-documenting infrastructure.
The admin panel HTML contains similarly over-documented opening comments:
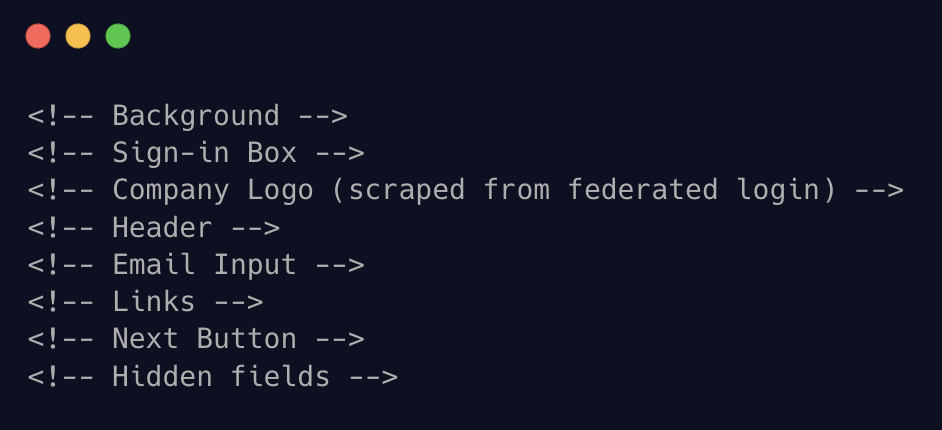
One of the Okta cloned login pages observed by Push contained the following comments suggesting the use of an LLM to create the clone:
The cloned Microsoft login pages displayed previously contain terser comments, but still typical of useless comments that are included by an LLM rather than a human author, especially a malware/phishing author:
The broken duplication in the heartbeat variant — where an inline script and client.js independently schedule the same backend requests using slightly different data formats — is consistent with an operator pasting requirements into an LLM and accepting the output without understanding the existing codebase well enough to recognize the redundancy.
Clearly, the barrier to entry for building (or forking) and operating a real-time vishing phishing panel is lower than the effectiveness of the tooling might suggest.
Infrastructure clustering and attribution
Through analysis of phishing domains, hosting infrastructure, and technical indicators in the panel source code, we’re highlighting four distinct infrastructure clusters associated with this tooling. While the panels share common heritage, the operators deploying them appear to be separate groups with different infrastructure preferences and operational patterns.
Cluster A
The indicators for Cluster A overlap with Mandiant’s reporting on UNC6661. Mandiant also attributes the extortion activity following UNC6661 intrusions to UNC6240, aka ShinyHunters.
Tool | Doko’s Panel |
client.js | 8a01bcb70ec1c101a163c9cb8e074781c1322096f7ae01789f02252854def44c f574b6e6b3a968cda5f51bec2c090d8eb095fbcfc383314f94bc15676a0d6692 |
Timeframe | November 2025 - present (April 2026) |
Domain Patterns | <target>internal.com <target>sso.com my<target>.com my<target>internal.com my<target>manager.com my<target>sso.com |
Examples | mydropboxinternal.com (November 2025) myxerointernal.com (December 2025) amazoninternal.com (March 2026) mydisneysso.com (March 2026) |
Registrar | NiceNIC |
Name Servers | 1984.is FreeDNS |
Hosting Provider | Mevspace (AS201814) |
Cluster B
The indicators for Cluster B overlap with Mandiant’s reporting on UNC6671. Other external reporting has linked this group to BlackFile-branded extortion and leaks.
Tool | heartbeat/check_redirect variant |
client.js | c0df36ccf88d5c8434b13b58f7a55a9715643a126148b9d078a93075d09cad26 d178dc7108fa9344dae28e350e810352e9e874563496dc7876ee628b11b0eabb 9c0939960e49122196e44b6779fe55dd7a13ab437ce251c8cf35f8c6daf8be21 e8128b33259f7ea4313c942689ba0ba557f17b1474f2e621c62a5b77674fab86 |
Timeframe | January 2026 |
Domain Patterns | <target>internal.com <target>sso.com my<target>sso.com |
Examples | epicgamessso[.]com (December 2025) myadyeninternal[.]com (January 2026) mysonossso[.]com (January 2026) sonosinternal[.]com (January 2026) |
Registrar | Tucows |
Name Servers | Njalla |
Hosting Provider | Njalla (AS39287) |
Cluster C
Cluster C is likely an evolution of Cluster B. Some evidence has been observed tying the backend hosting to Njalla behind the Cloudflare CDN further solidifying the link. The shift to Cloudflare Turnstile protection and subdomain-based targeting represents an operational refinement — moving away from the distinctive [target]internal[.]com pattern that had become a well-known campaign indicator.
Tool | heartbeat/check_redirect variant Protected with Cloudflare turnstile |
client.js | cb1d409278b2247af23e7b00ac779b232baaf4ce5f63fdf5ebc3920a38cc6102 |
Timeframe | March 2026 - present (April 2026) |
Domain Patterns | <target> subdomain with generic “sso”, “passkey”, “enroll”, “okta” theme root domain |
Examples | <target>.passkeysetup.com (March 2026) <target>.enrollms.com (March 2026) <target>.keyokta.com (April 2026) <target>.passkeywork.com (April 2026) |
Registrar | Tucows |
Name Servers | Cloudflare |
Hosting Provider | Cloudflare (AS13335) |
Cluster D
Tool | heartbeat/check_redirect variant (minified) |
client.js | 9d65dd34384b441505e6b67647153c02d5c367bb53da36ce36a392e70b37940a |
Timeframe | April 2026 (low volume) |
Domain Patterns | <target> subdomain with generic “passkey”, “portal”, “okta” theme root domain |
Examples | <target>.passkeyportalsetup.com <target>.addoktapasskey.com |
Registrar | NiceNIC |
Name Servers | Cloudflare |
Hosting Provider | Cloudflare (AS13335) |
Detection considerations
For Push, the detection approach to these panels is fundamentally the same as for any other phishing kit — behavioral analysis of the rendered page in the browser, regardless of the C2 protocol running underneath.
The main operational difference is on the operator end, where the human-in-the-loop interaction replaces fully automated credential harvesting. This has implications for defenders relying on proactive infrastructure scanning: the gated landing pages, anti-bot checks, and operator-approval requirements mean the malicious content is only served to active targets, making it significantly harder for automated scanners to discover and flag these domains before they're used against a victim.
The phone call as delivery vector eliminates the email-based detection surface that most organizations rely on as their primary phishing defense. Combined with the operator-gated payload delivery, this means that unless you are detecting the phishing page at the point where it renders in the victim's browser — analyzing page structure, credential entry behavior, and phishing kit signatures in real time — these attacks will reach their targets unimpeded.
Indicators of compromise
Short-lived IoCs are of limited value when tackling modern phishing attacks due to the rate at which attackers are able to quickly spin up and rotate the sites used in the attack chain, often dynamically serving different URLs to site visitors.
Bulk list of domains to be follow, check back later.
Push customers do not need to take any further action.
Learn more about Push
Push Security is the most powerful AI-native security tool in the browser. Think EDR, but for the browser — high-fidelity telemetry and real-time control across every session, on every device, with no browser migration required. Security teams use Push to detect and stop advanced browser-based attacks like AiTM phishing, ClickFix, and session hijacking; gain visibility and control over AI tool usage across their workforce; harden identities by surfacing credential reuse, SSO gaps, and shadow IT; and support data loss and insider investigations with browser-layer telemetry that other tools can't see. Book a live demo to learn more.

