What is a third-party integration?
In the Push platform, a third-party integration is an application that uses the OAuth authorization standard to connect with your Microsoft 365 or Google Workspace instance to grant some level of access to your deployment’s data.
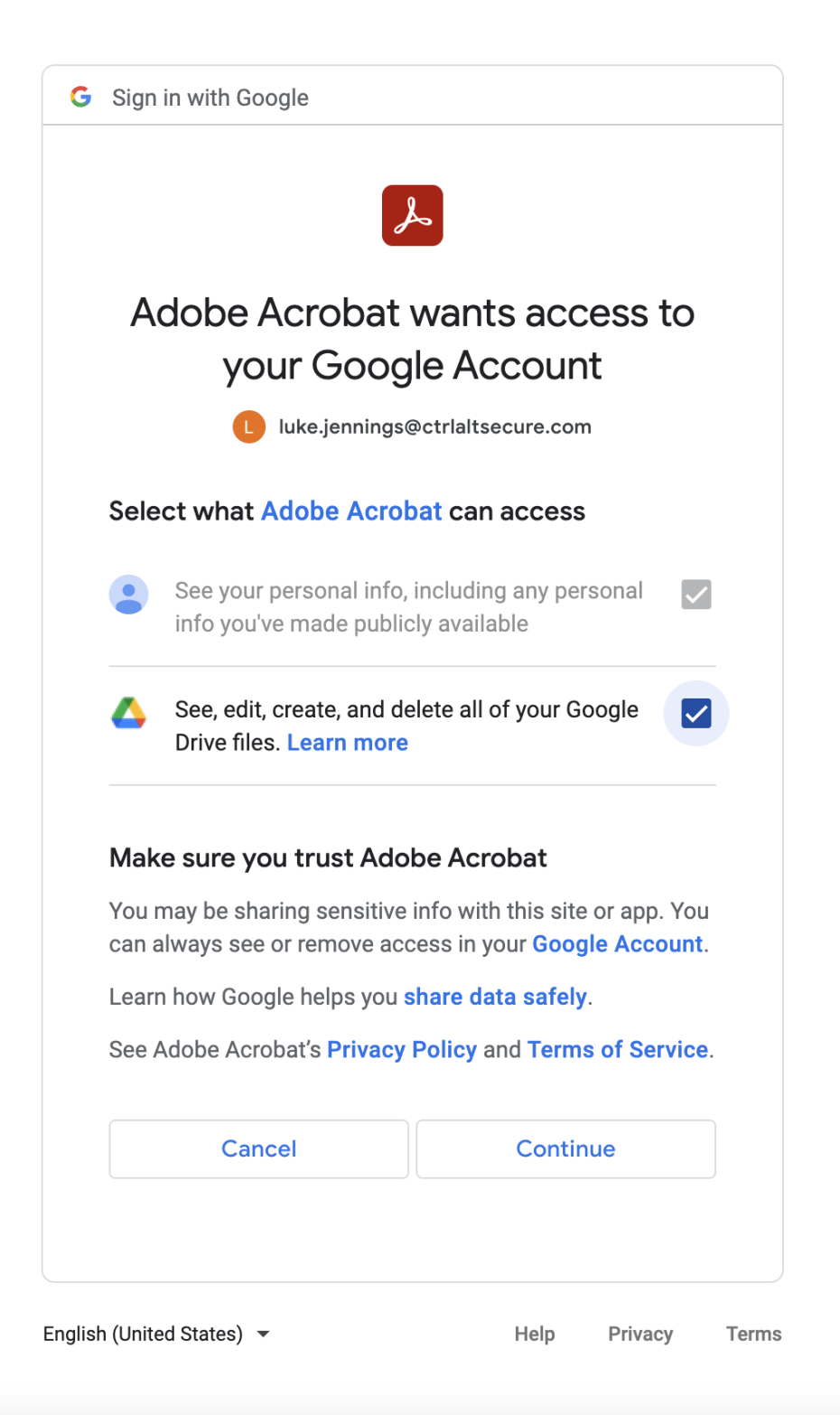
This can be as simple as sharing an employee’s full name and email address with the SaaS application in order to complete a login using Sign In with Google and Sign In with Microsoft, a mechanism known as a social login.
Third-party integrations can also be granted more wide-ranging permissions, such as access to a user’s calendar to add meetings, or the ability to access, edit, create, and delete all of your Google Drive files, for an app that manages file sharing.
What type of third-party integration activity does Push capture?
Once you complete an API integration with the Push platform and your work platform (Microsoft or Google), you’ll see third-party integration activity, which includes whether the publisher of an integration is verified and the integration’s risk characteristics, as well as how many users have consented to an integration and when it was last used.
The Push browser extension also captures social login activity as soon as it's observed.
When is third-party integration usage recorded?
Usage is recorded when the integration is used. This is often not the same as when the underlying application is used.
For example, if you have granted Google social login scopes to an application, the integration is only used when you click "Sign In with Google." Since many apps go on to cache your identity, it is common for these integrations to not be used for weeks or even months after, even if you regularly use the application you’re logging into.
Are third-party integrations safe?
Third-party integrations are generally a secure way to connect different applications and boost employee productivity. However, you should consider whether you’re comfortable with the given third-party having access to the data that has been granted.
For guidance on assessing the security of third-party integrations, refer to the Push blog post Is it safe to allow my employees to connect third-party apps to our M365/Google Workspace tenant?
To learn more about social logins, which can bring security benefits to your organization, refer to our blog post Should I let my employees log in with their work Google account?