Stop account takeover
Account takeover usually looks like a normal login. Push monitors authentication directly in the browser, exposing the access paths attackers rely on, from ghost logins to credential stuffing, before damage is done.
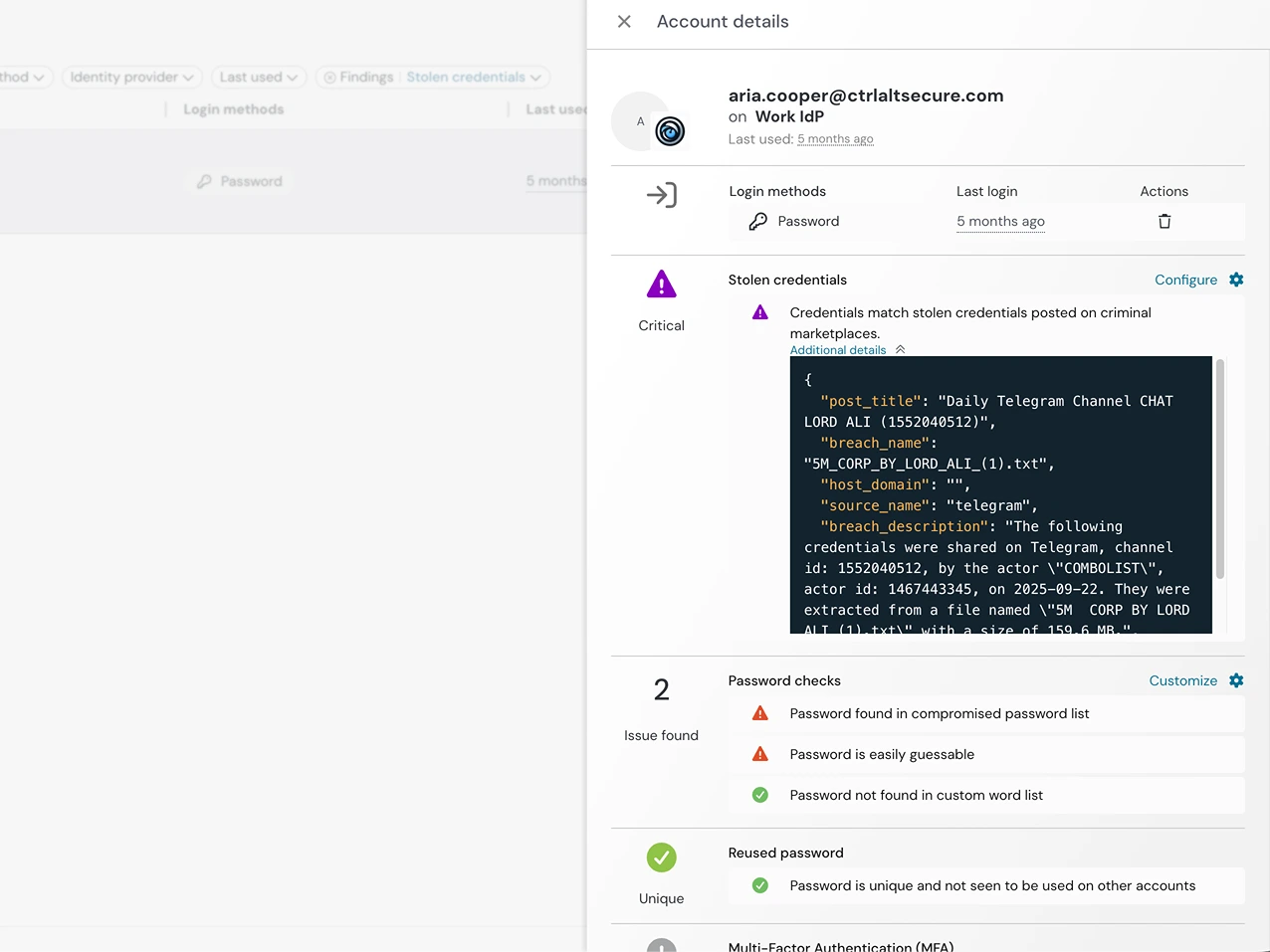
- Identify credential-based ATO as it unfolds
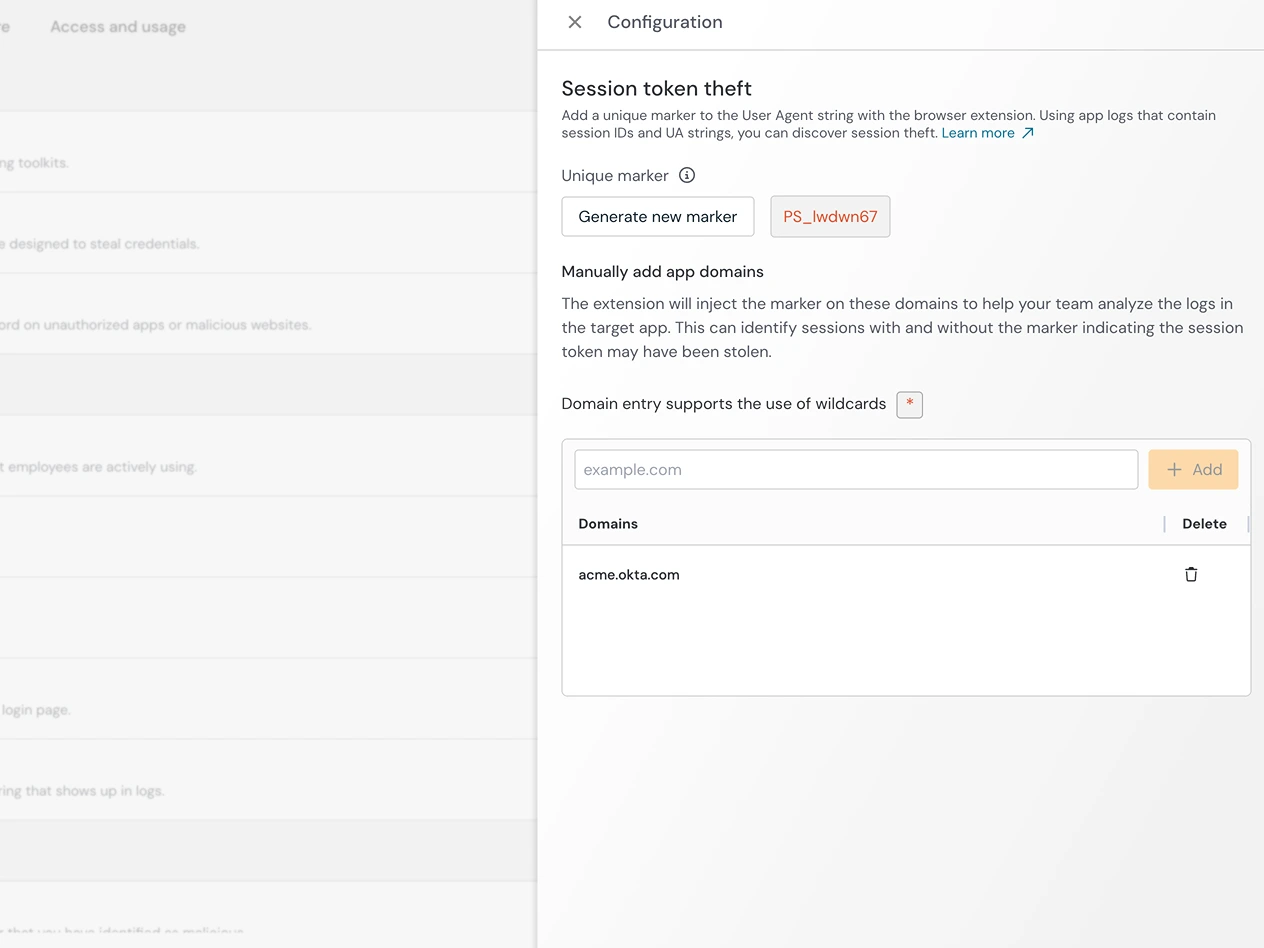
- Surface hijacked sessions and token misuse
- Strengthen authentication security where your IdP can’t